Limit permission to delete resources by time period
Limit EC2 delete permissions by time period
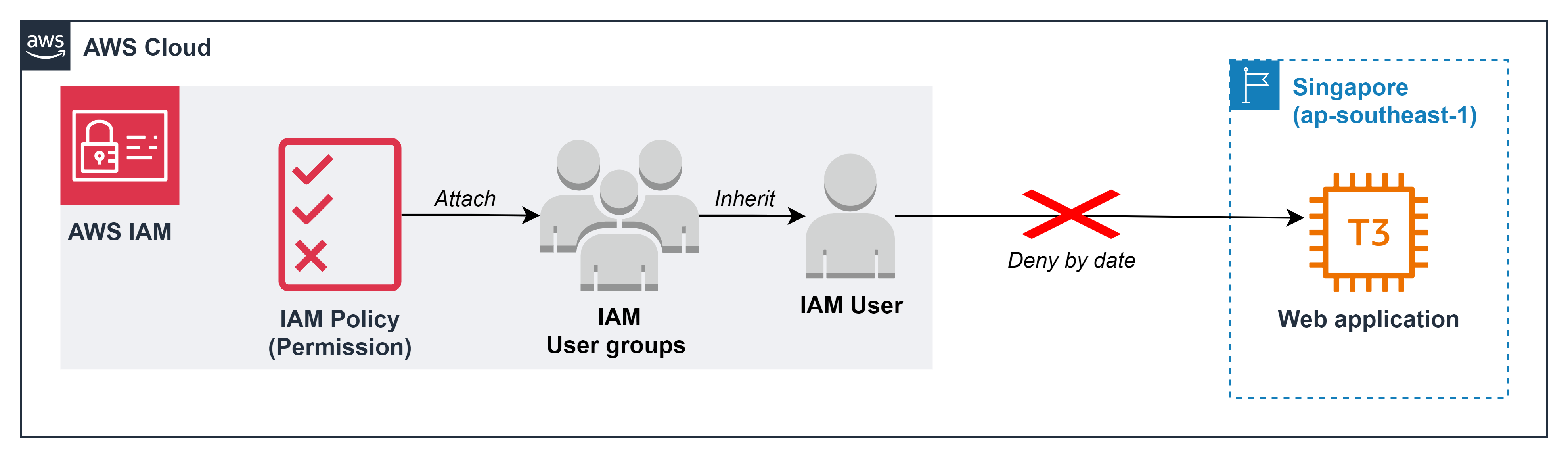
At some important times of the year, such as holidays, black Friday, audit time,… the system needs to operate effectively to ensure it serves the business’s goals. Therefore, as a cloud admin and criteria of zero trust, you need to ensure that there are no unexpected resource deletion incidents during the above times.
So we will practice this lab based on the time of January 26, 2026
Create IAM Policy
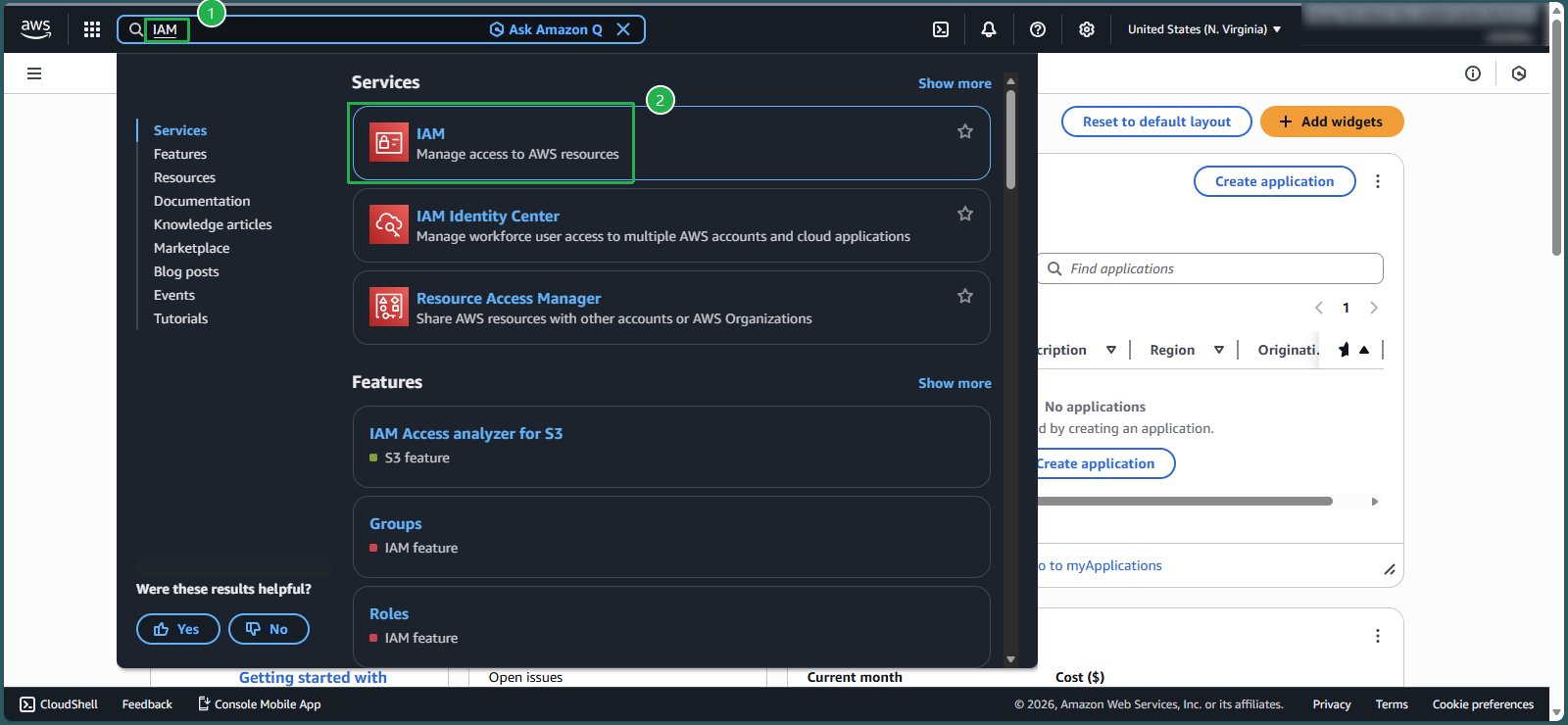
- In the AWS console, in the search box, enter
IAM - Select IAM service
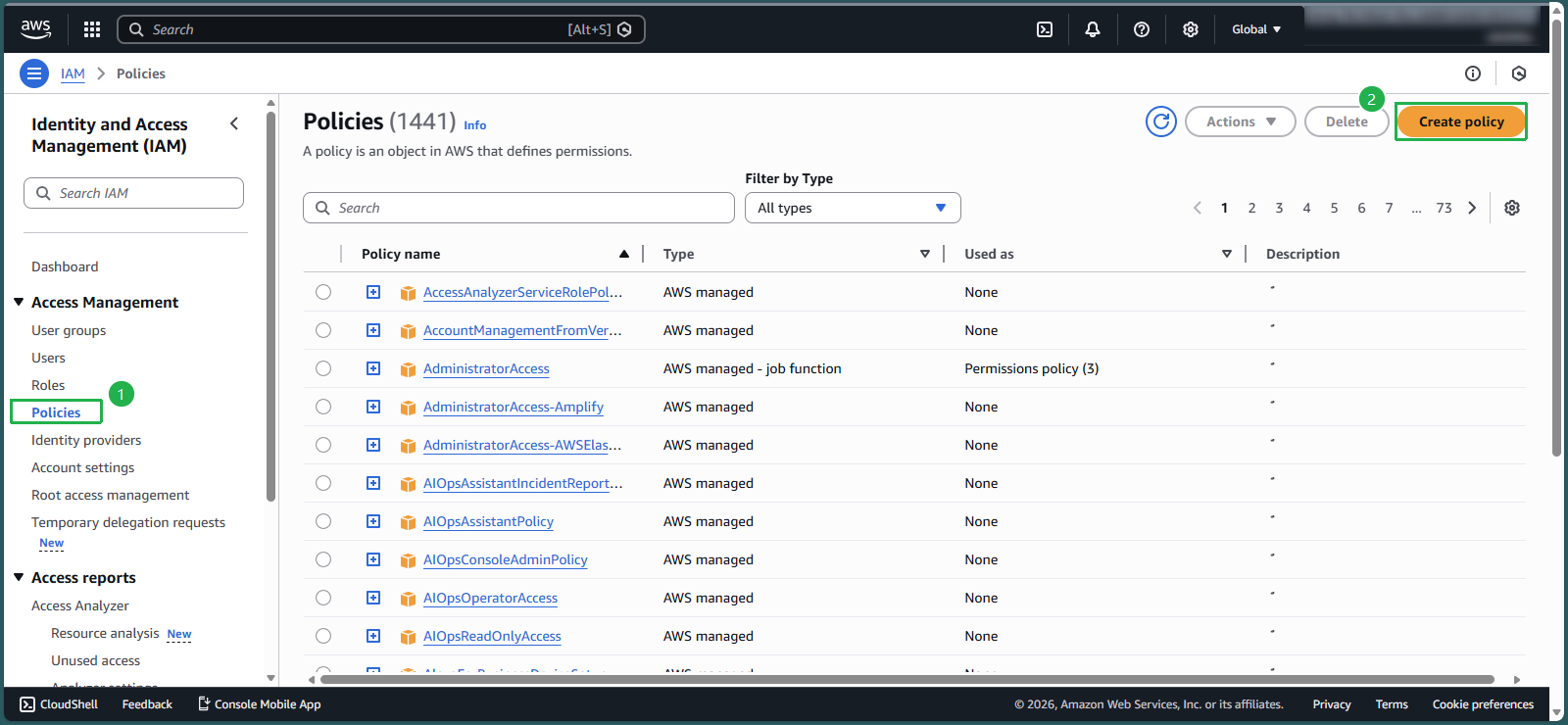
- On the left side of the screen, select
Policies - Select Create policy
Create policy in JSON data format instead of Visual. Select
JSONScan the entire current code and press the Delete button
Copy the following code into the Policy editor box.
Noted: With format yyyy-mm-dd and timezone as UTC, you need:
- Change the value in the DateGreaterThan line to 2026-01-25
- Change the value in the DateLessThan line to 2026-01-27
- -> You must change the timelines above to correspond to the time you are doing the lab to achieve the desired results.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "VisualEditor0", "Effect": "Deny", "Action": "ec2:TerminateInstances", "Resource": "arn:aws:ec2:*:148922931563:instance/*", "Condition": { "DateGreaterThan": { "aws:CurrentTime": "2026-01-25" }, "DateLessThan": { "aws:CurrentTime": "2026-01-27" } } } ] }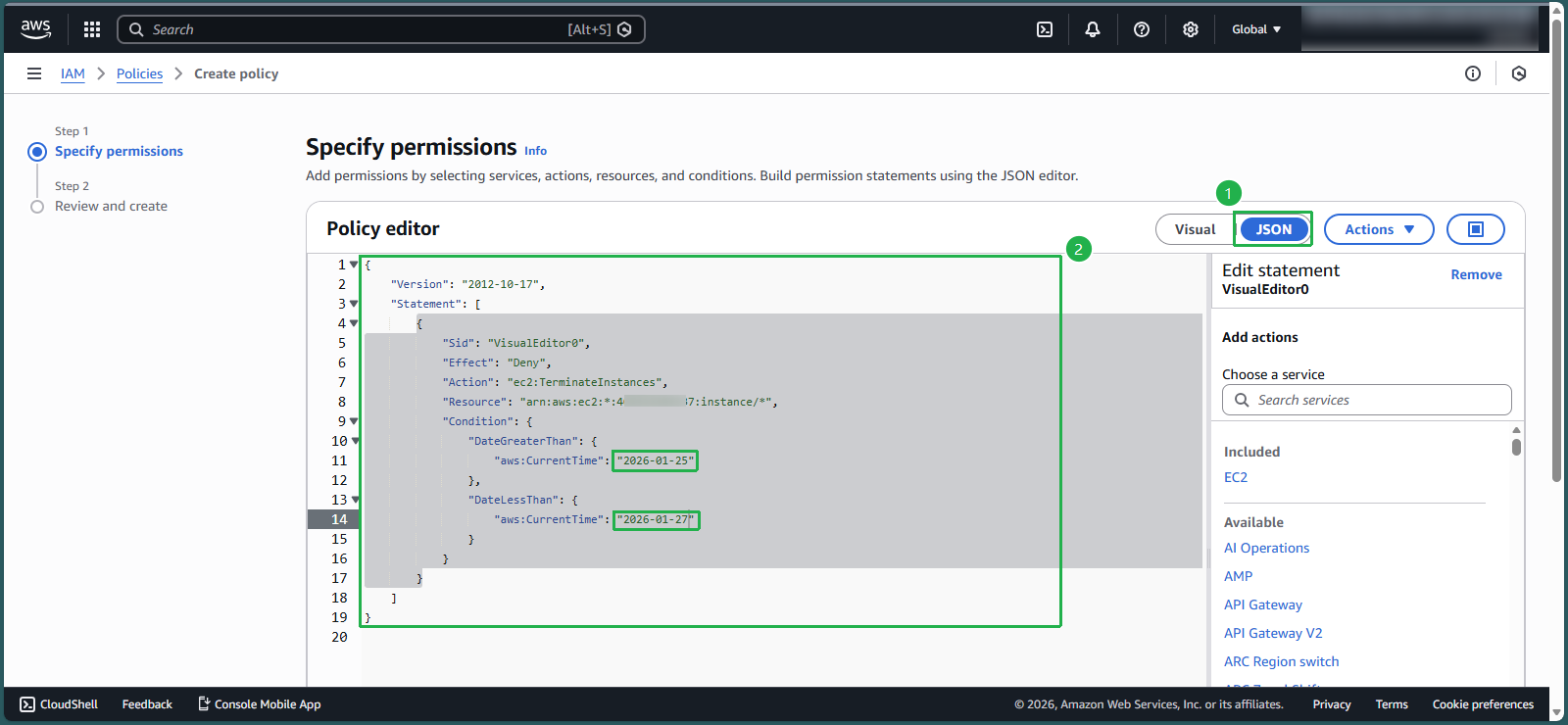
Scroll down and select Next
In the Policy name section, enter:
EC2_TimeRestrictIn the Description section, enter:
Restrict terminate EC2 in one week
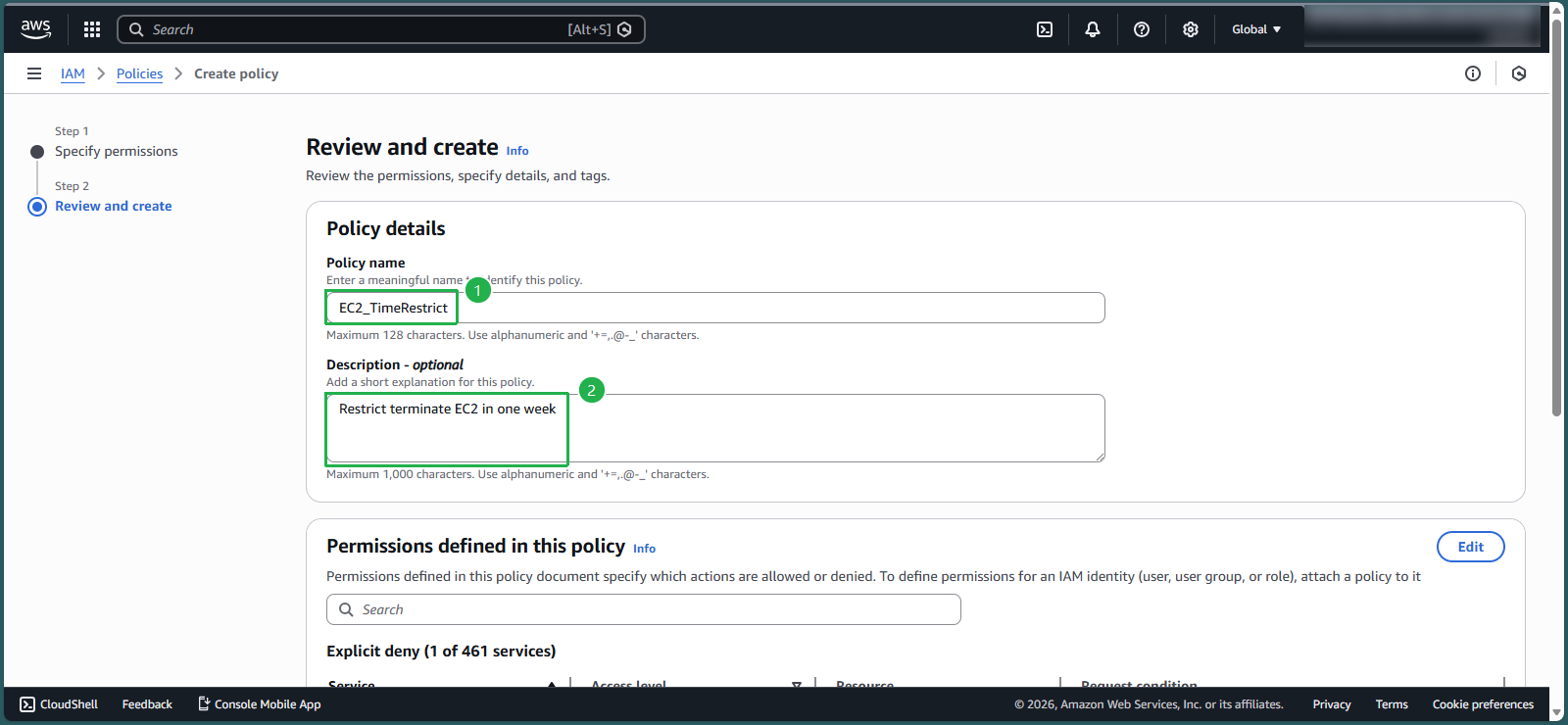
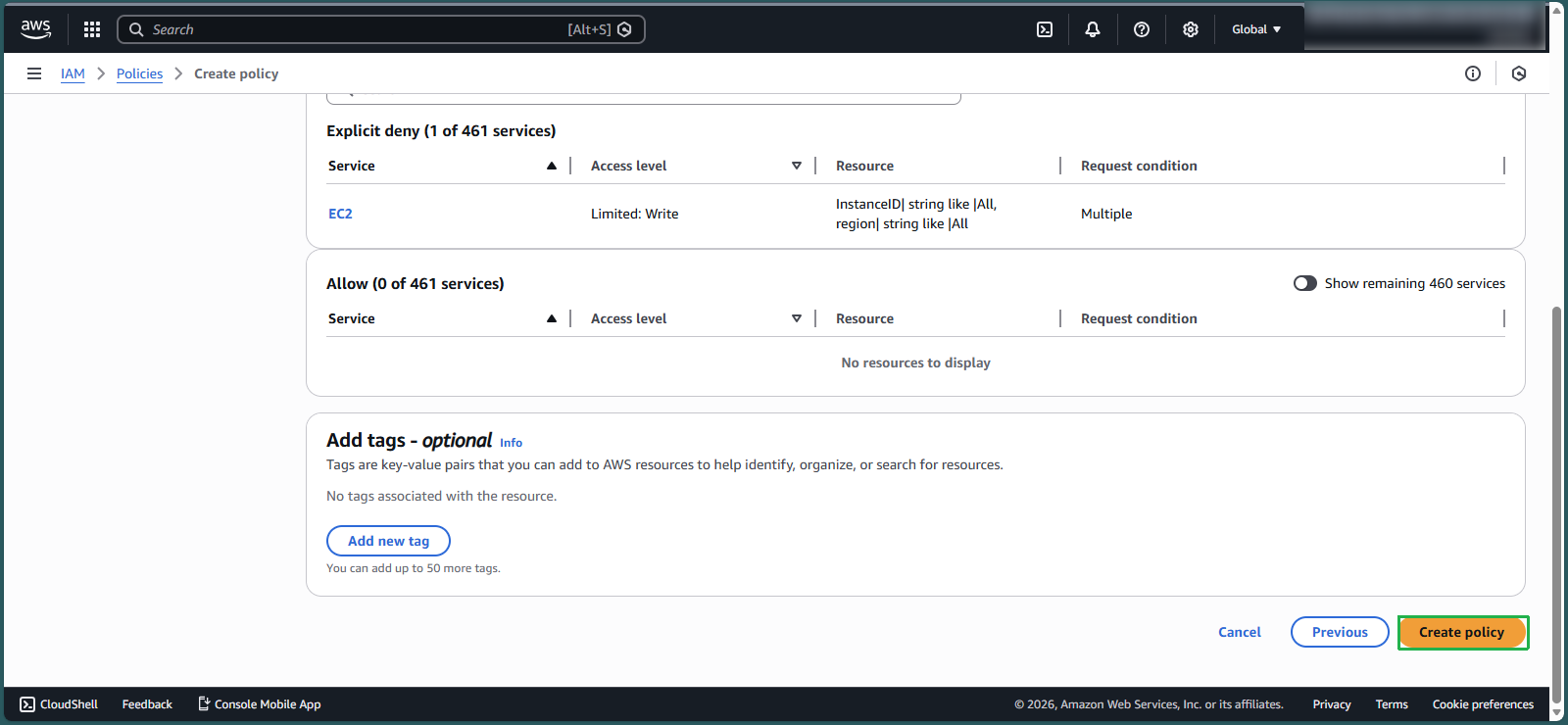
- Scroll to the bottom of the page and select Create policy
- In the AWS console, in the search box, enter
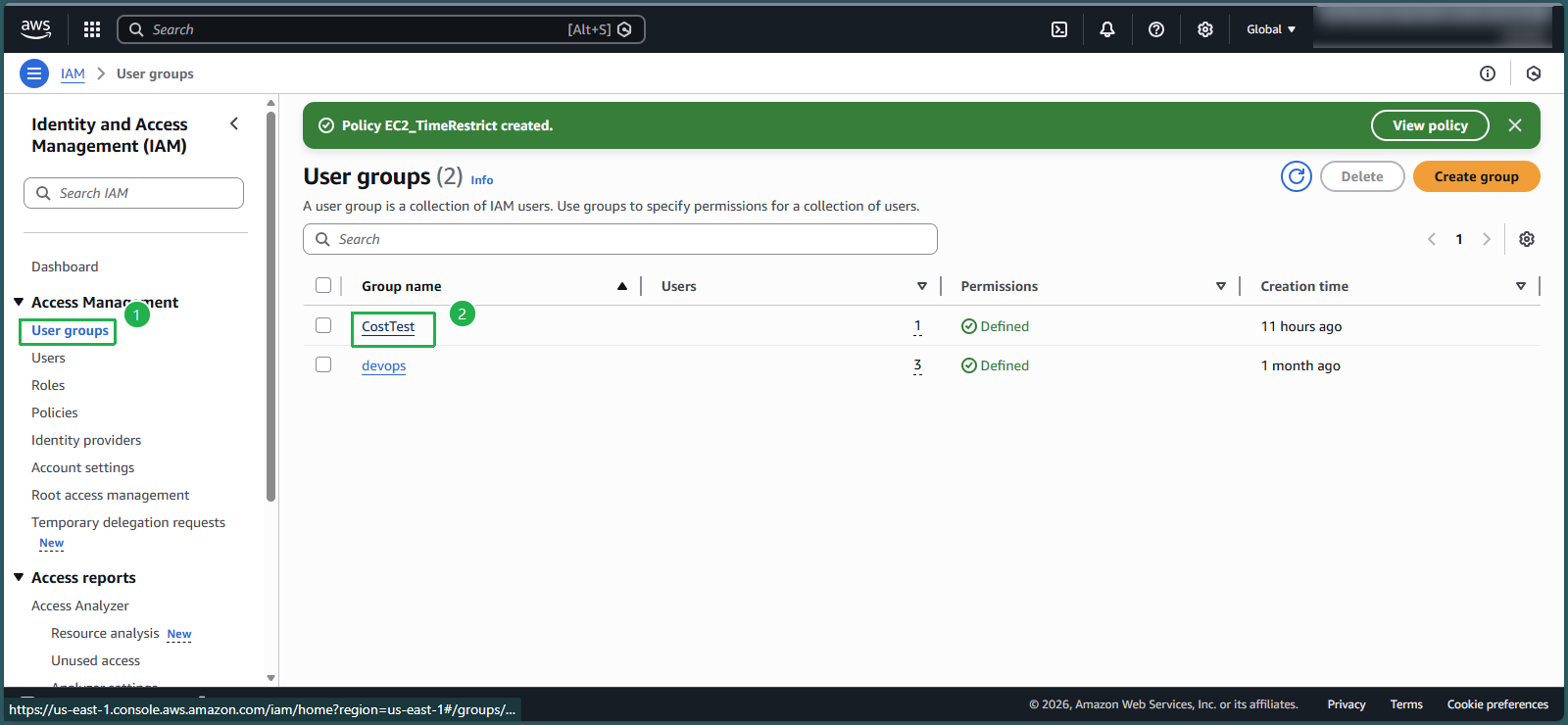
Add policy EC2_TimeRestrict to group CostTest
- At IAM Console, left section - select User groups
- Select CostTest
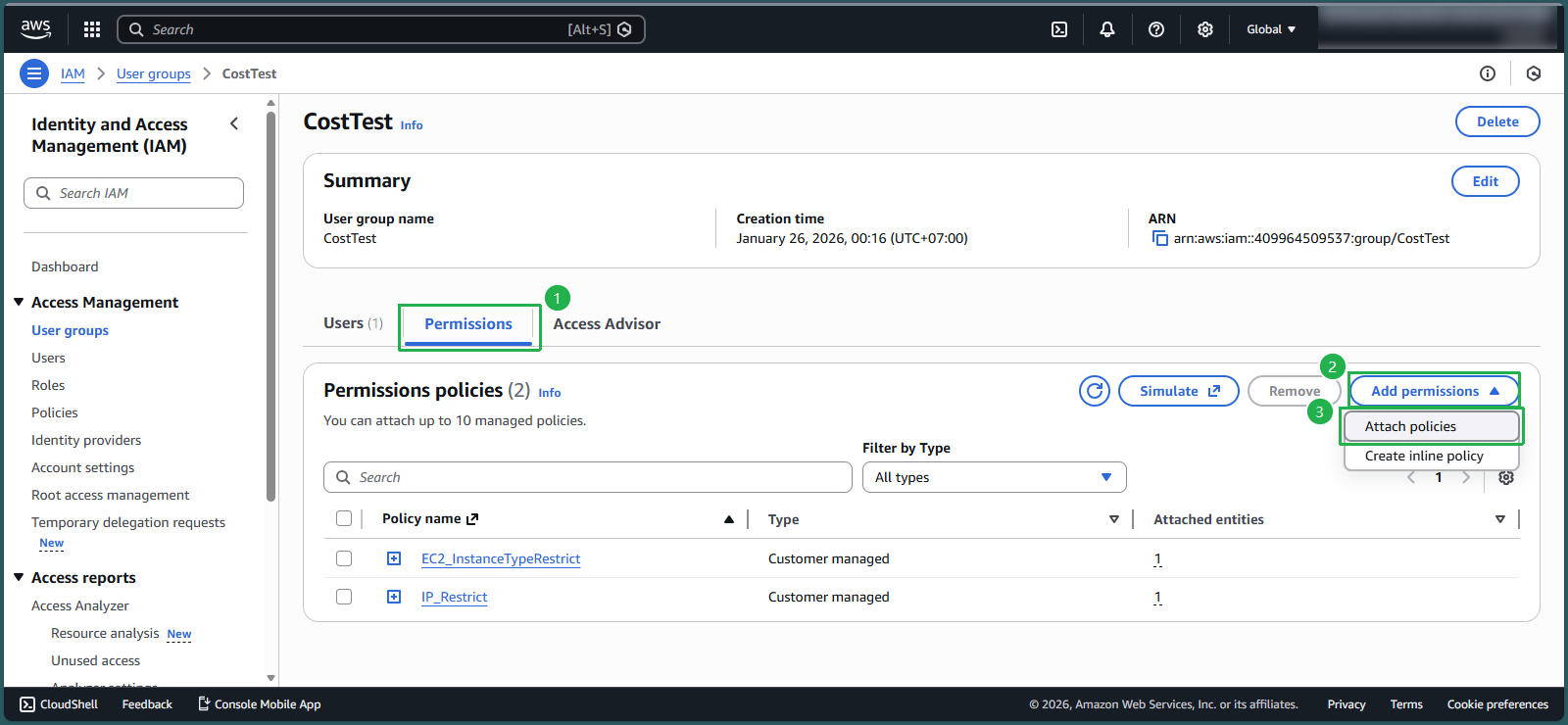
- Select Permissions
- Select Add permissions, select Attach policies
- In the search box 🔍, enter
EC2_TimeRestrict. - Check the box symbol □ to select a policy, select Attach policies
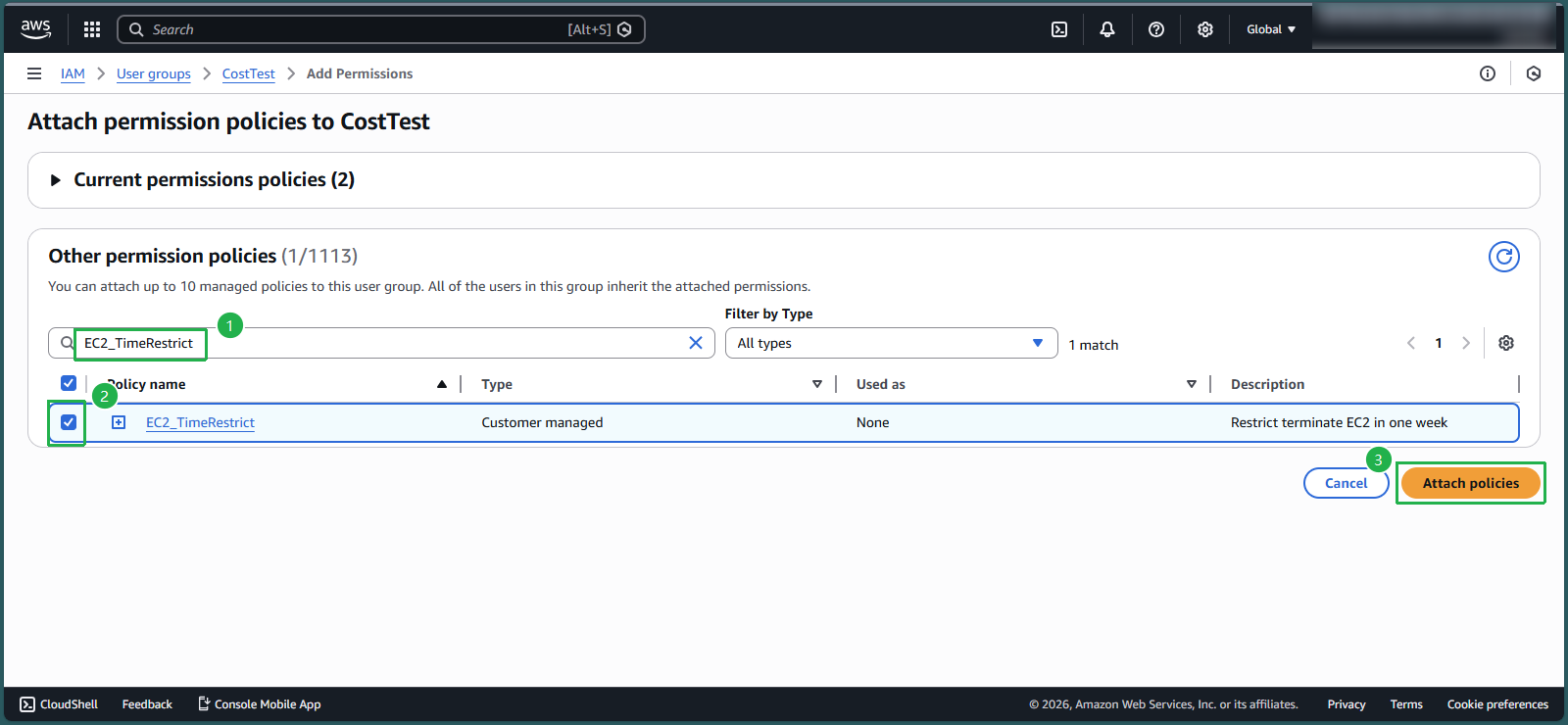
- Check Permissions policies
- Now in the CostTest group there is policy EC2_TimeRestrict, policy IP_Restrict and policy EC2_InstanceTypeRestrict that you created in lab 8.3
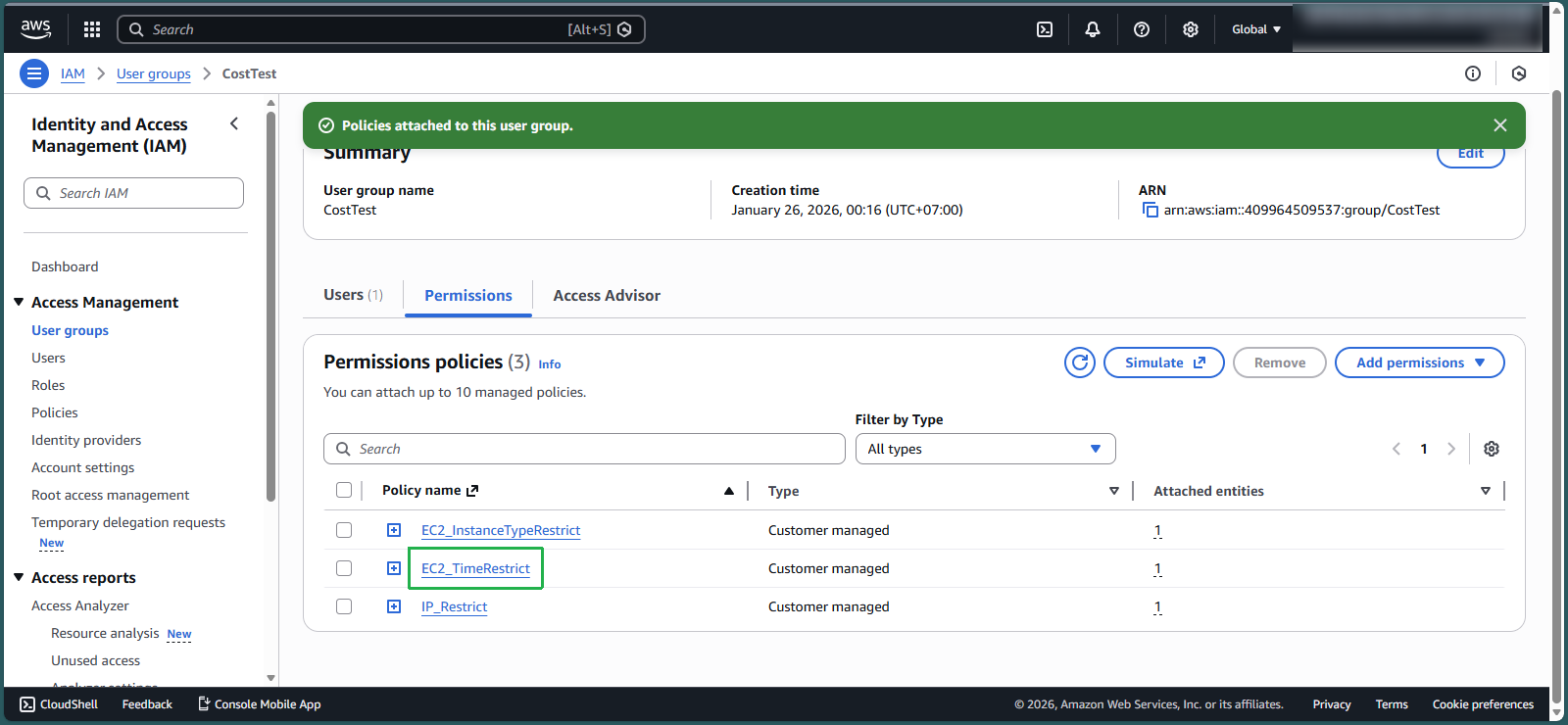
Check Permissions policies
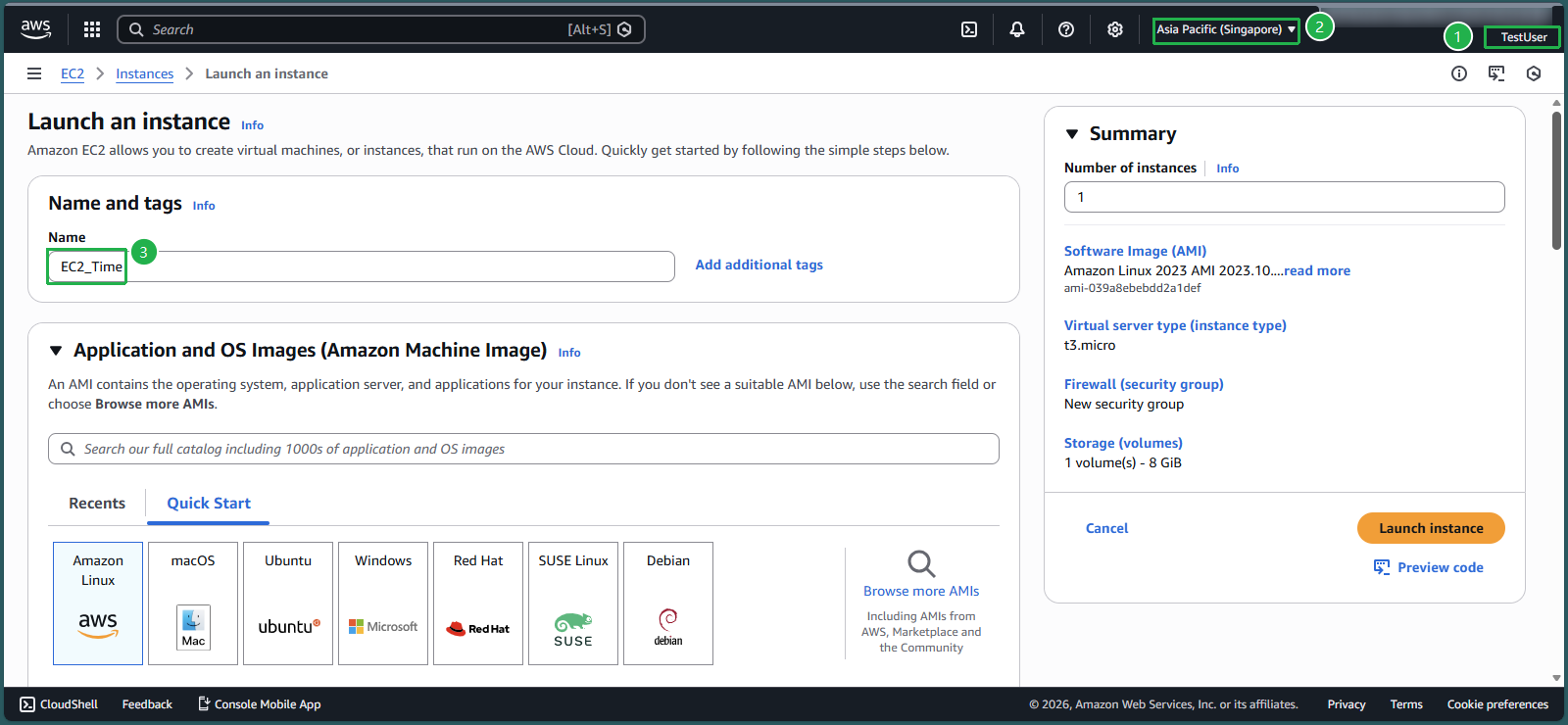
- Log in to TestUser with the information you created in lab 8.1, step 4
- Make sure you are in Region Singapore
- In the search box 🔍, enter
EC2 - At the EC2 interface, in the middle of the page, select Launch instance
- In the Name section, enter
EC2_Time
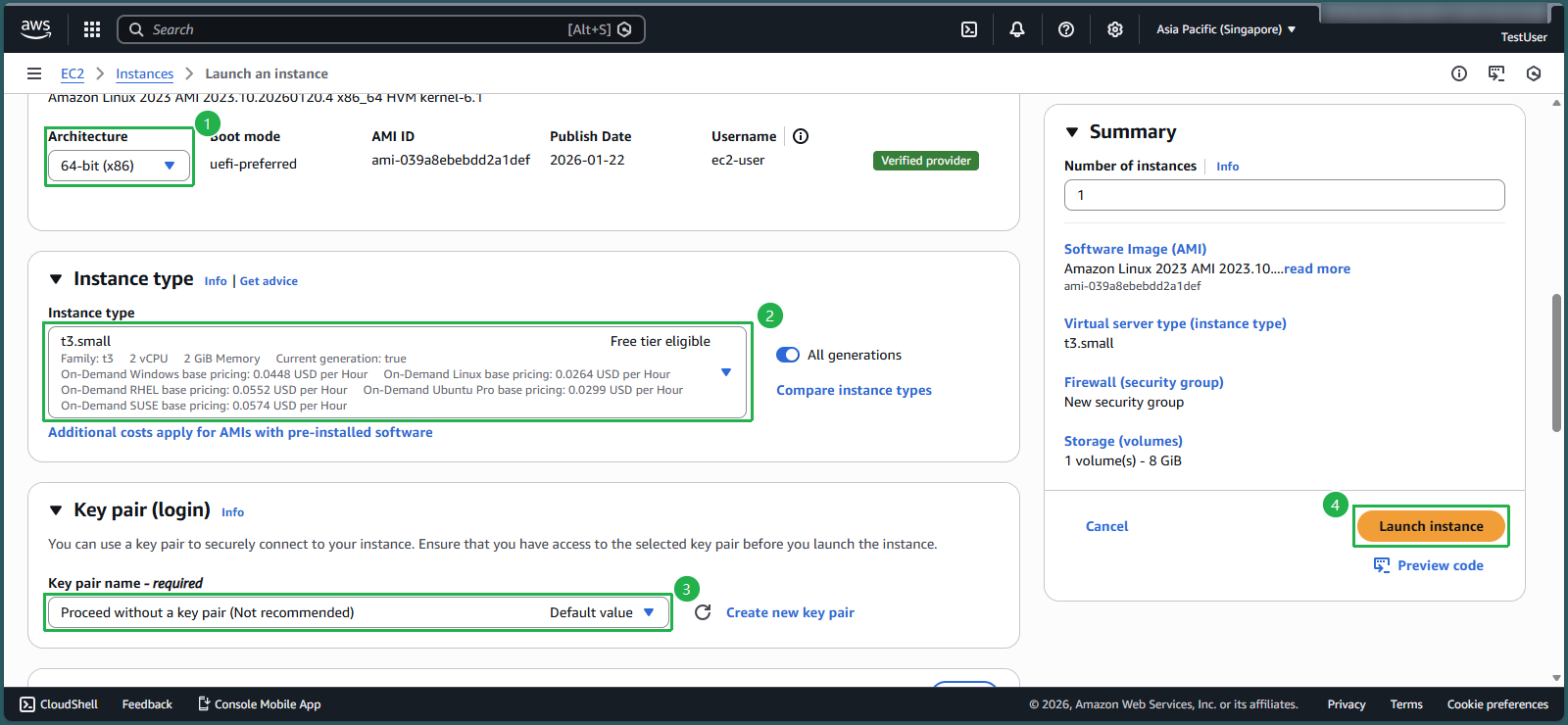
- In the Architecture section, keep the value 64-bit (x86)
- In the Instance type section, select the triangle symbol, enter
t3.small - In the key pair name section, select the triangle symbol, select Proceed without a key pair (Not recommended)
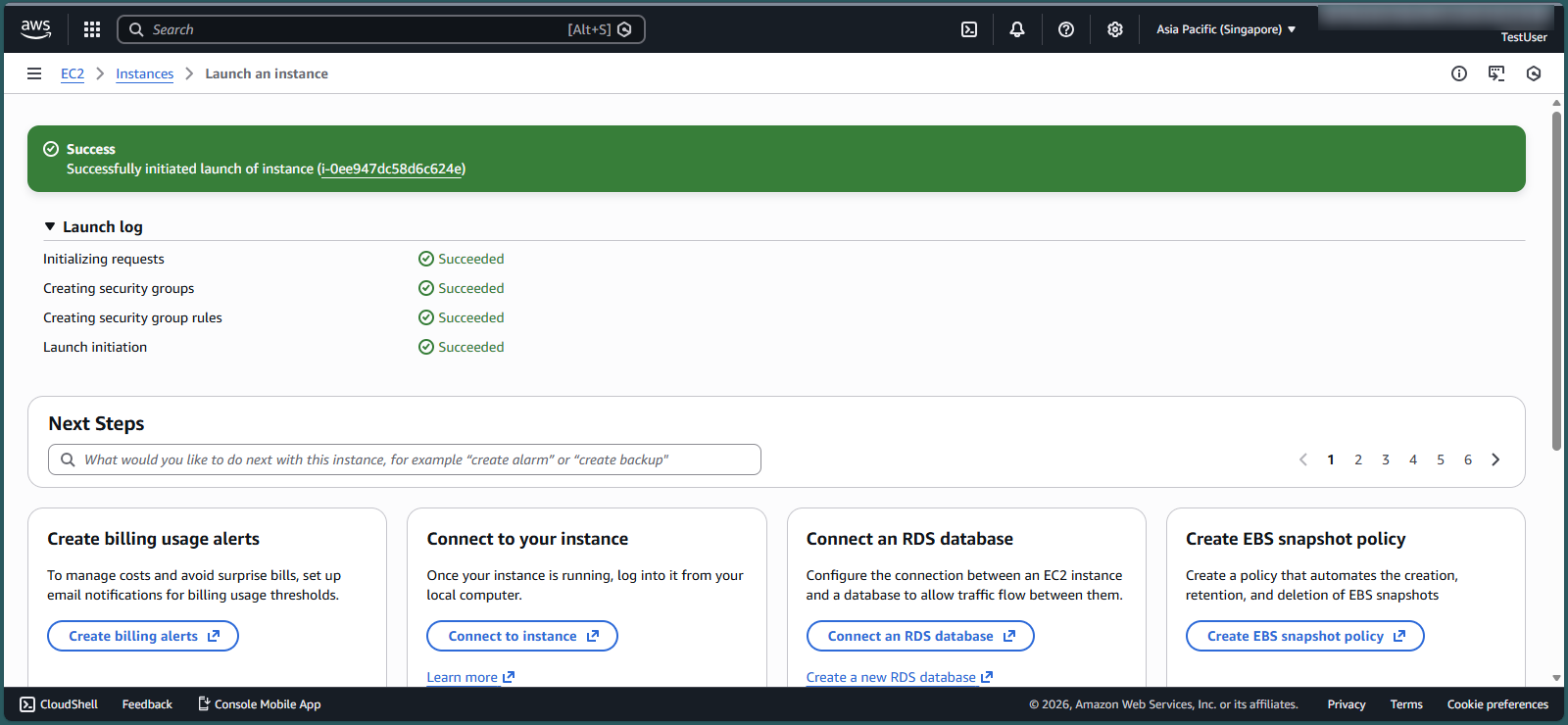
- Select launch instance
- Select Instance ID that has just been successfully created
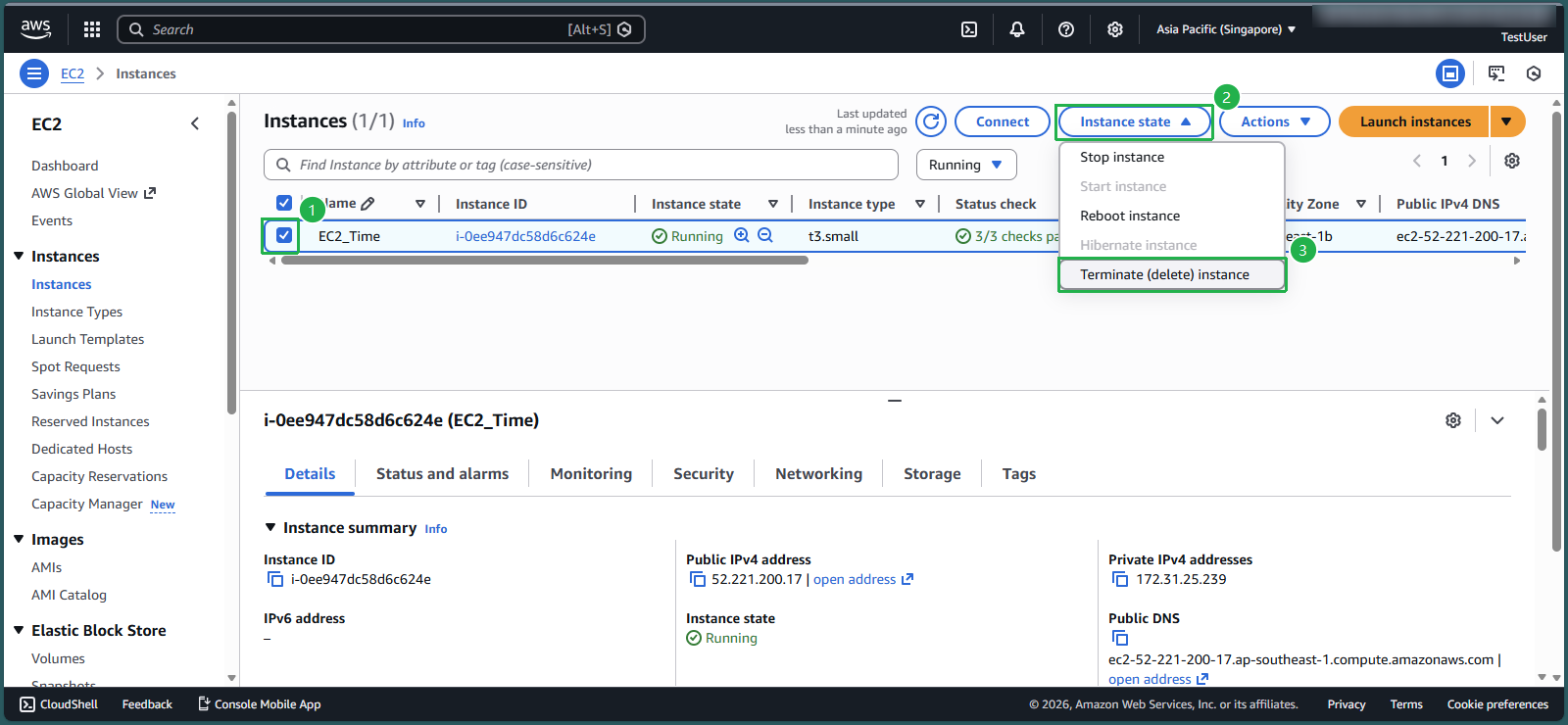
- Check the box symbol to select EC2 instance
- Select Instance state
- Select Terminate instance
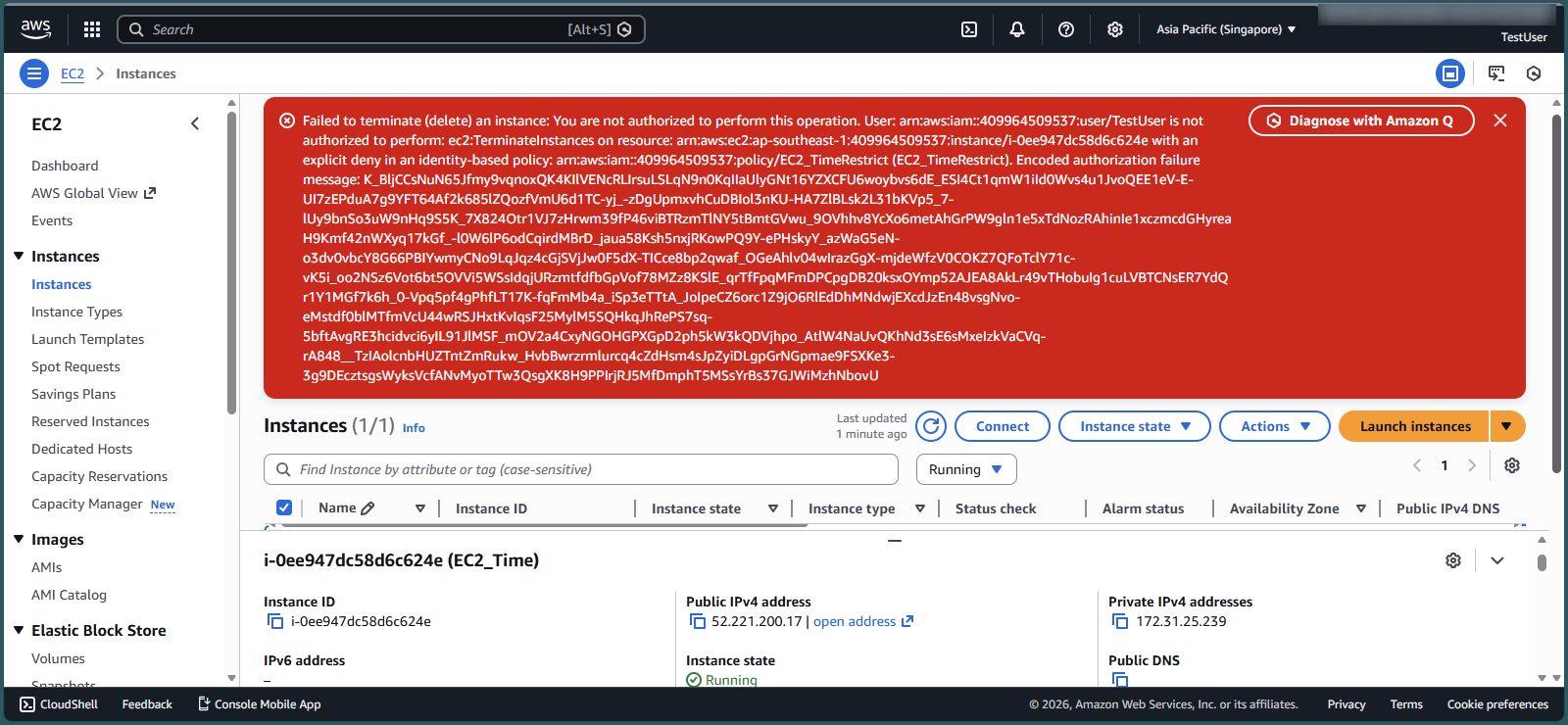
- The system reports an error as shown in the picture because you are not authorized to delete EC2. This demonstrates the success of your policy creation in step 1.
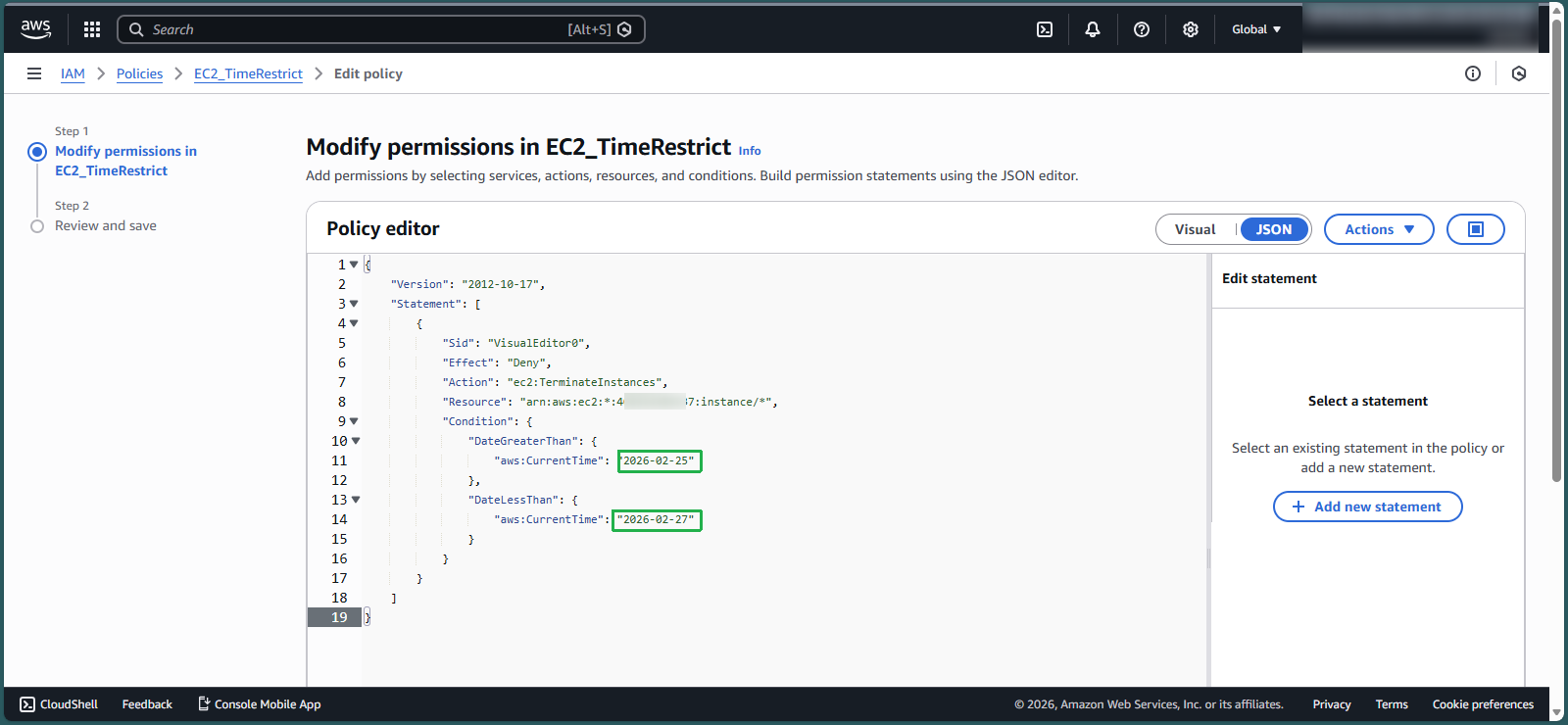
Check Permissions policies with a different time period
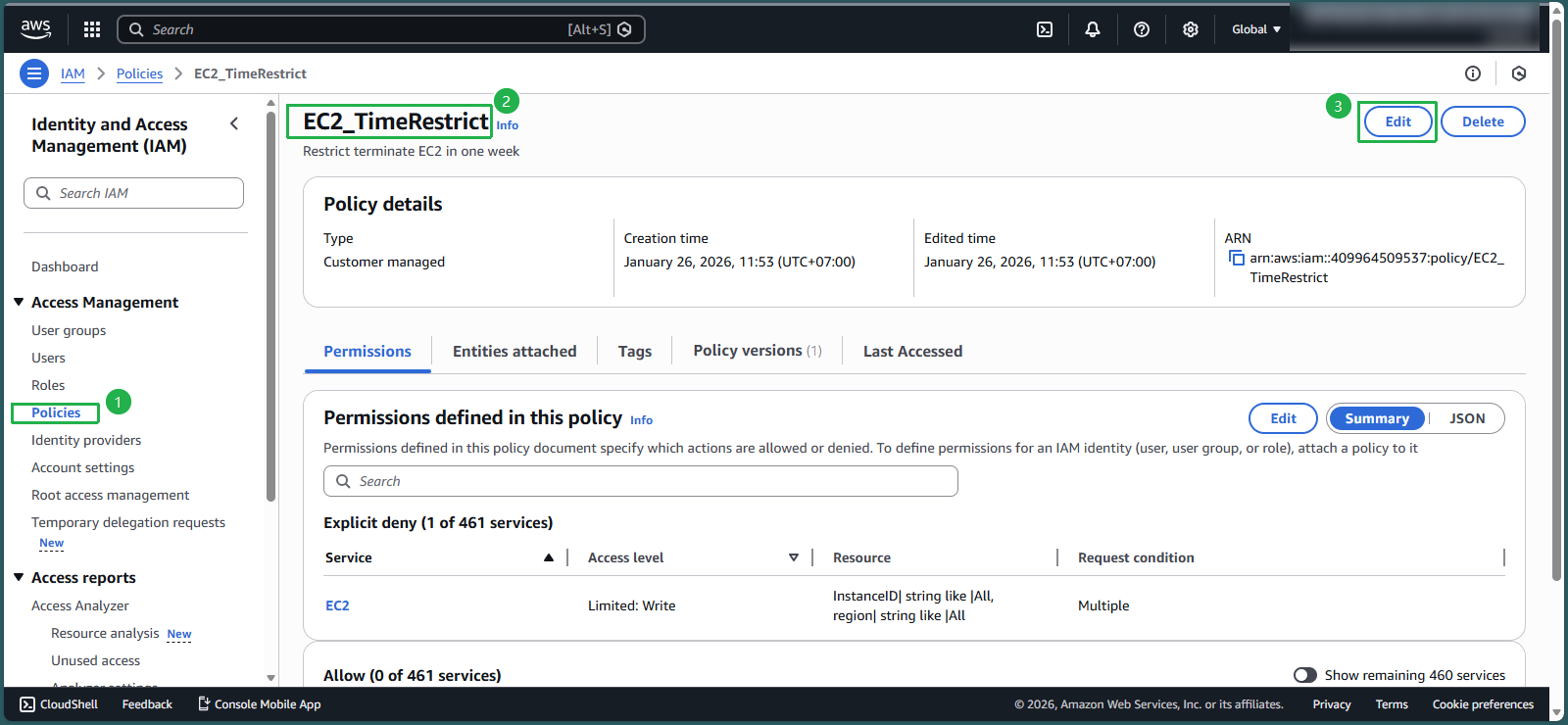
- In the IAM interface, select Policies
- In the search box, enter EC2_TimeRestrict
- Select EC2_TimeRestrict
- Select Edit
- With format yyyy-mm-dd and time zone UTC, you need:
- Change the value in the DateGreaterThan line to 2026-02-25
- Change the value in the DateLessThan line to 2026-02-27
- -> You move from January to February
- Select Next
- Scroll to the bottom of the page and select Save changes
- Return to the EC2 interface
- Check the box symbol to select the EC2 instance you created in step 3
- Select Instance state
- Select Terminate instance
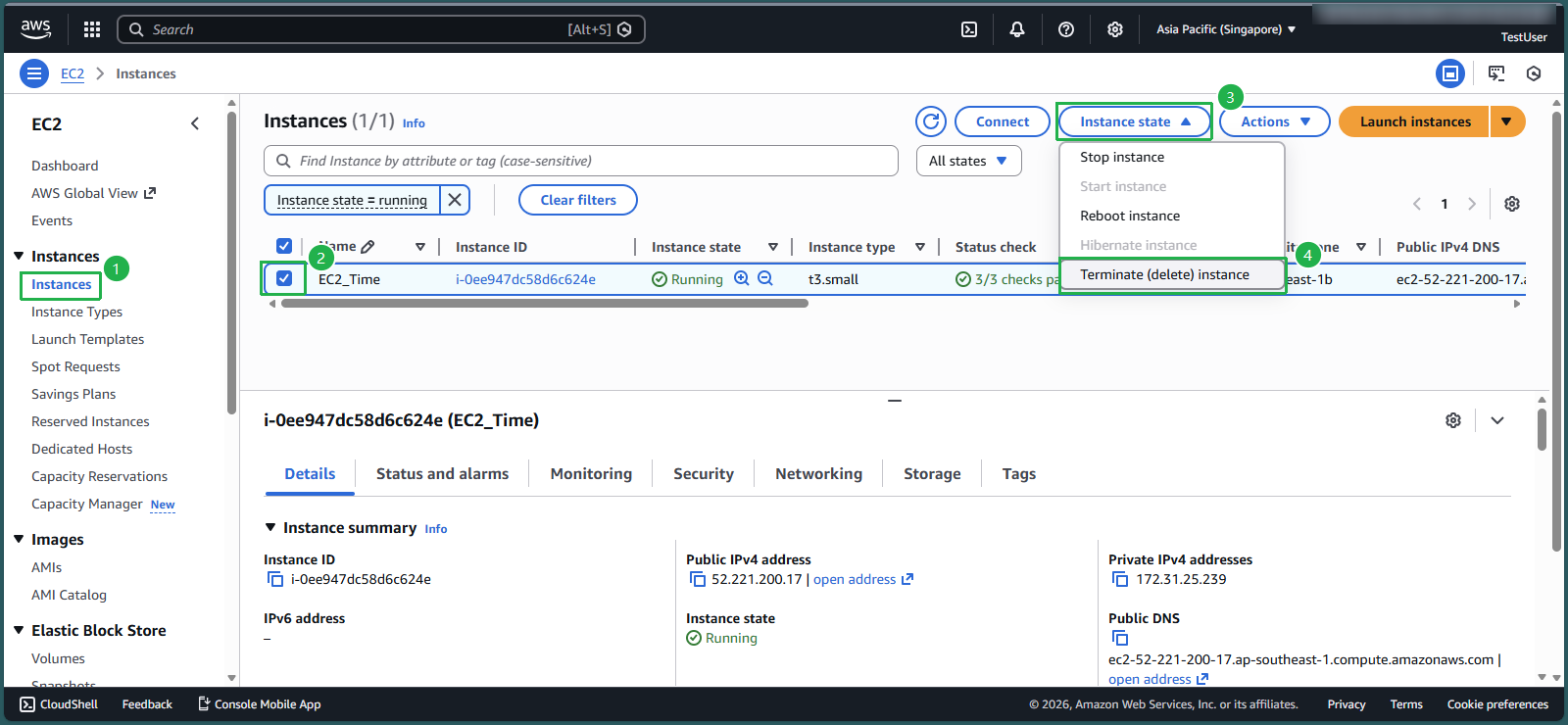
- Select Terminate
- Congratulations, you have successfully deleted EC2 when changing the time period.
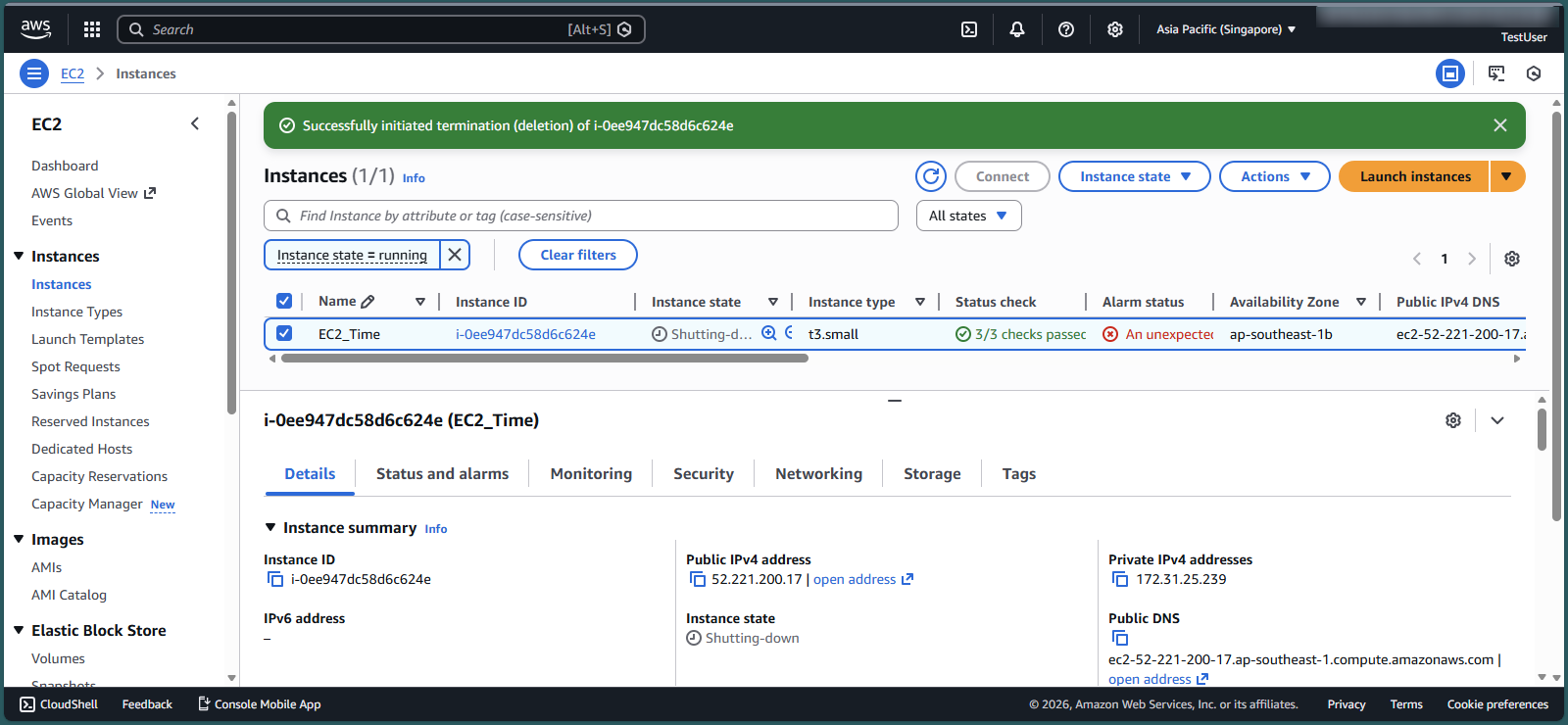
- In reality, we just need to remove this policy from the group to delete EC2 and when you need, just edit it again in time and add it to IAM User Group.