Limiting EC2 Usage by Instance Family
Implementing EC2 Instance Family Restrictions for Cost Optimization
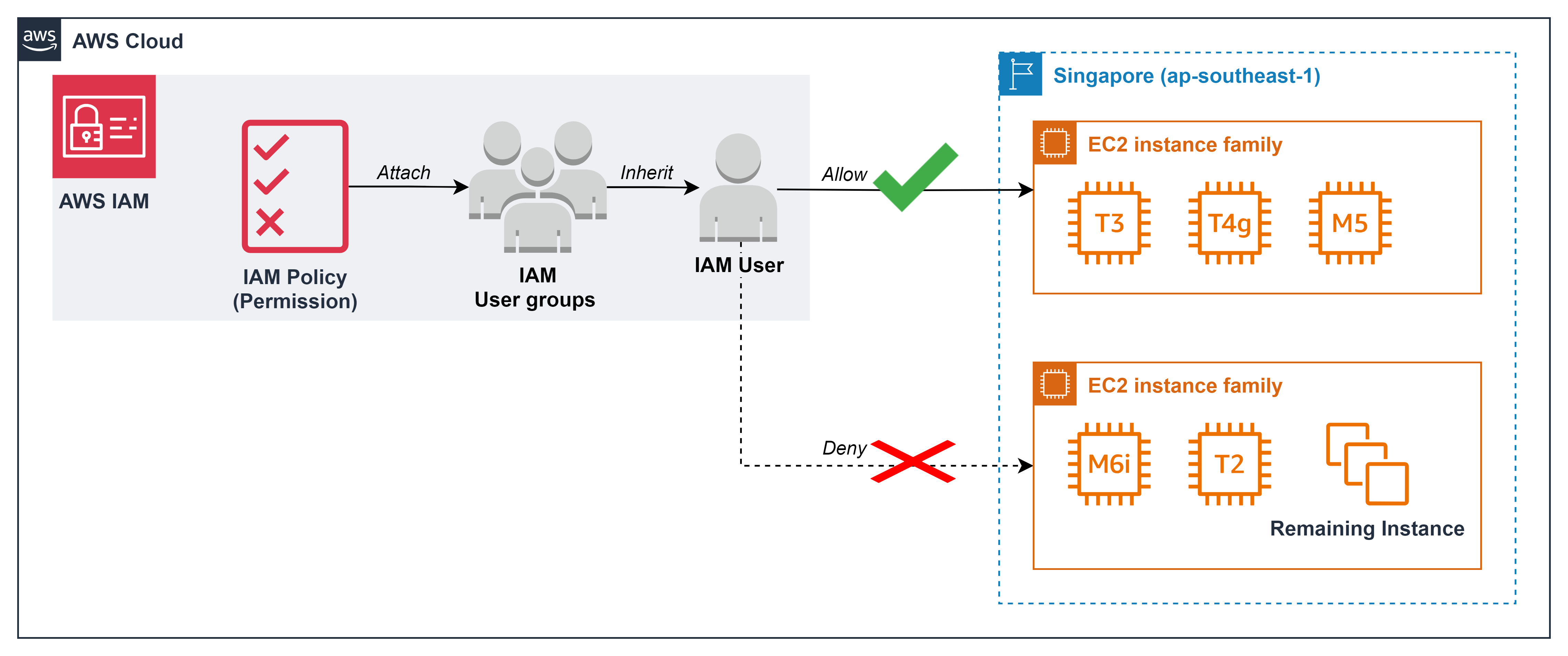
ℹ️ Information: AWS EC2 offers various instance families optimized for different workloads. By restricting which instance families users can deploy, organizations can implement effective cost governance while ensuring workloads run on appropriately sized resources.
Business Benefits of Instance Family Restrictions
- Prevents deployment of unnecessarily expensive instance types
- Aligns compute resources with actual workload requirements
- Simplifies instance selection for development teams
- Reduces cloud waste from over-provisioned resources
- Maintains performance standards while controlling costs
💡 Pro Tip: For development and testing environments, limiting users to cost-effective general purpose instances can significantly reduce your AWS bill while still providing sufficient resources for non-production workloads.
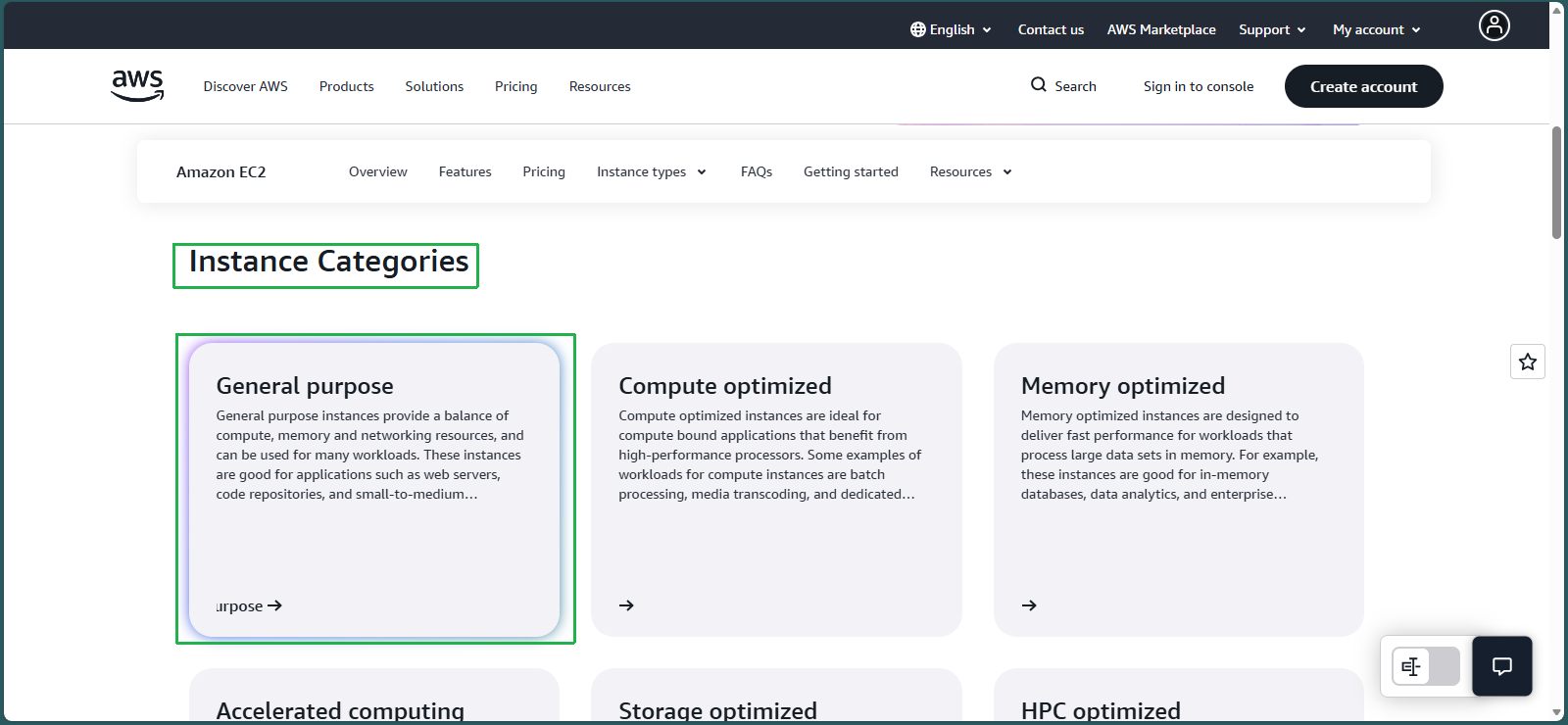
Understanding EC2 Instance Families
AWS organizes EC2 instances into families that target specific use cases:
- C – Compute optimized (high performance processors)
- R – Memory optimized (large memory-to-CPU ratios)
- M – General purpose (balanced resources)
- T – Burstable performance (variable workloads)
- G – GPU-based (graphics and machine learning)
For comprehensive information on all instance types, refer to the Amazon EC2 Instance Types documentation.
Implementation Steps
Analyze Compute Requirements
As a Cloud Engineer, you’ve received the following requirements from the Development team:
- Resources appropriate for development environments
- Support for both x86 and Arm CPU architectures
- Capability to run small and medium databases
- Sufficient resources for code repository solutions
- Focus on General Purpose instances for development phase
Select Appropriate Instance Families
- Navigate to the AWS EC2 Instance Types page
- In the Instance Categories section, select General Purpose
- In the Explore instance types section, review each instance family by examining:
- Key technology for processor types, performance characteristics, and capabilities
- Ideal use cases for recommended workloads and applications
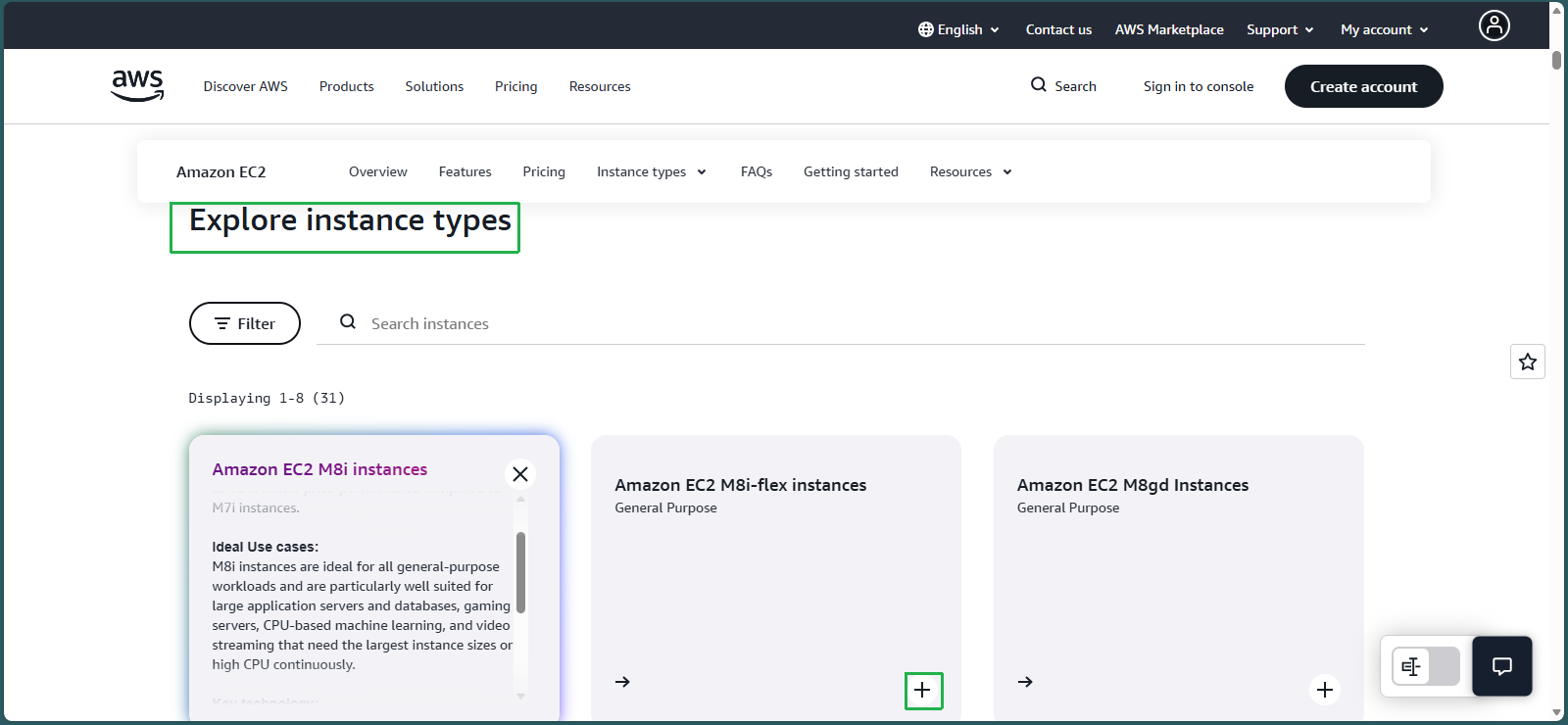
- Based on the requirements, select the following instance families:
- T3: x86-based, burstable performance, ideal for development
- T4g: Arm-based, cost-effective for development workloads
- M5: x86-based, balanced resources for databases and general workloads
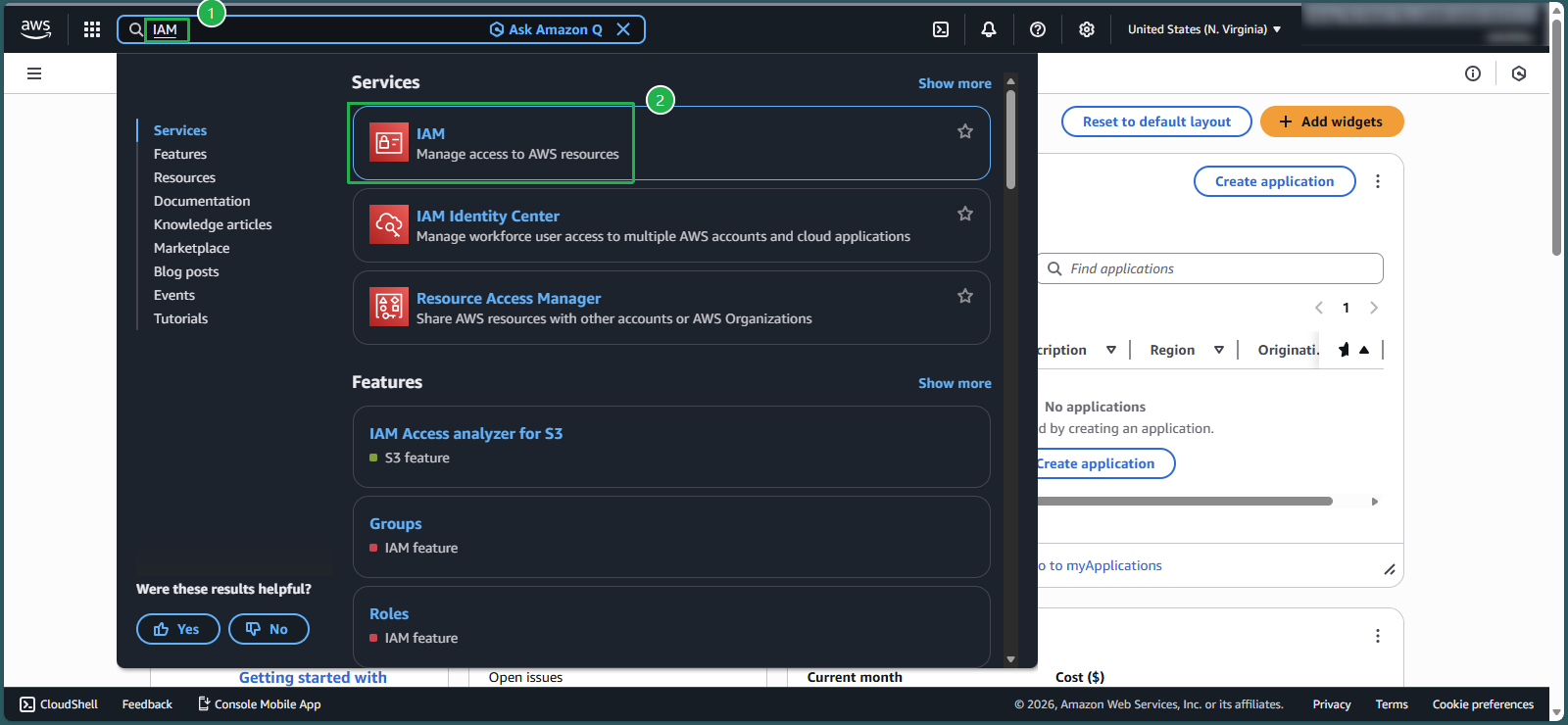
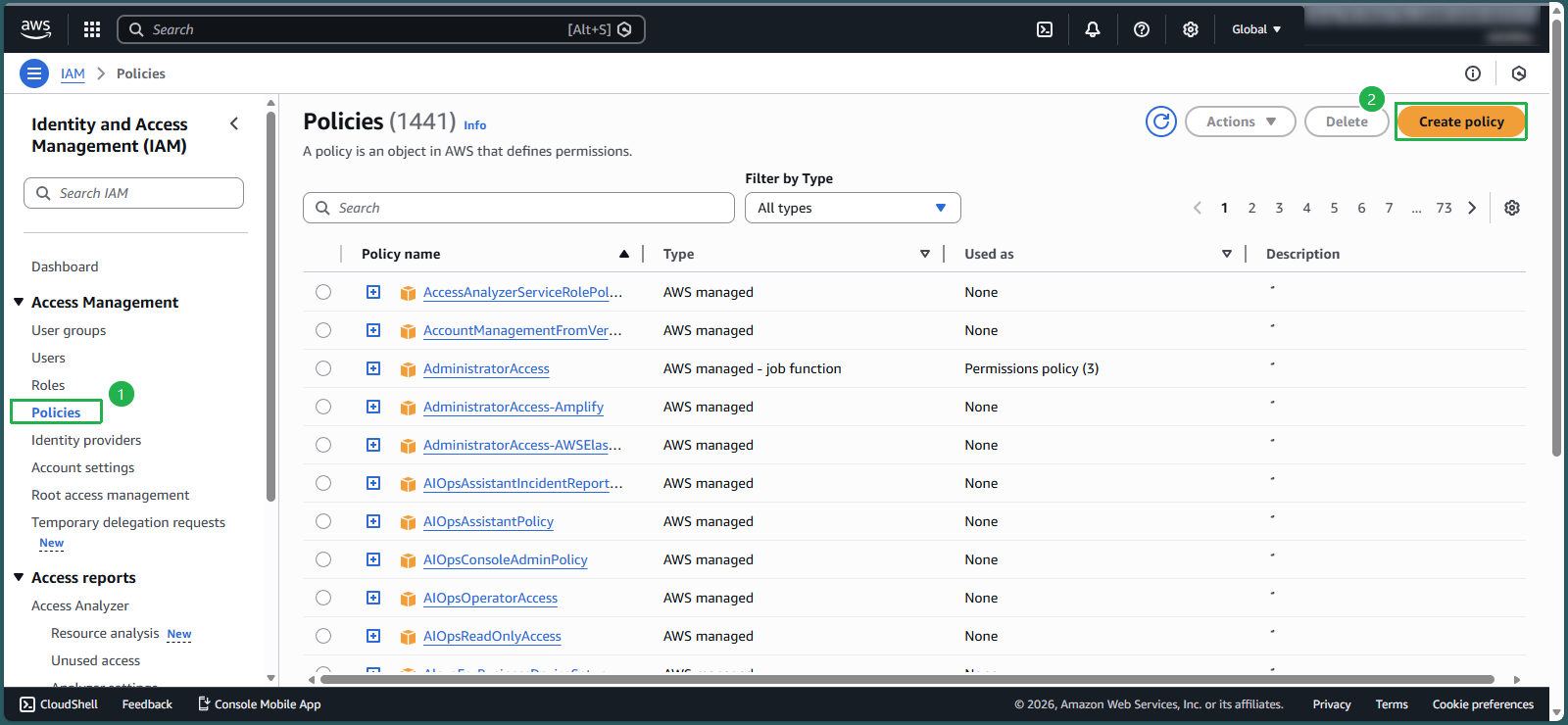
Create an IAM Policy for Instance Family Restriction
- In the AWS Management Console search box, enter
IAM - Select the IAM service
- In the navigation pane, select Policies
- Click Create policy
Switch to the JSON editor tab
Delete any existing template code in the editor
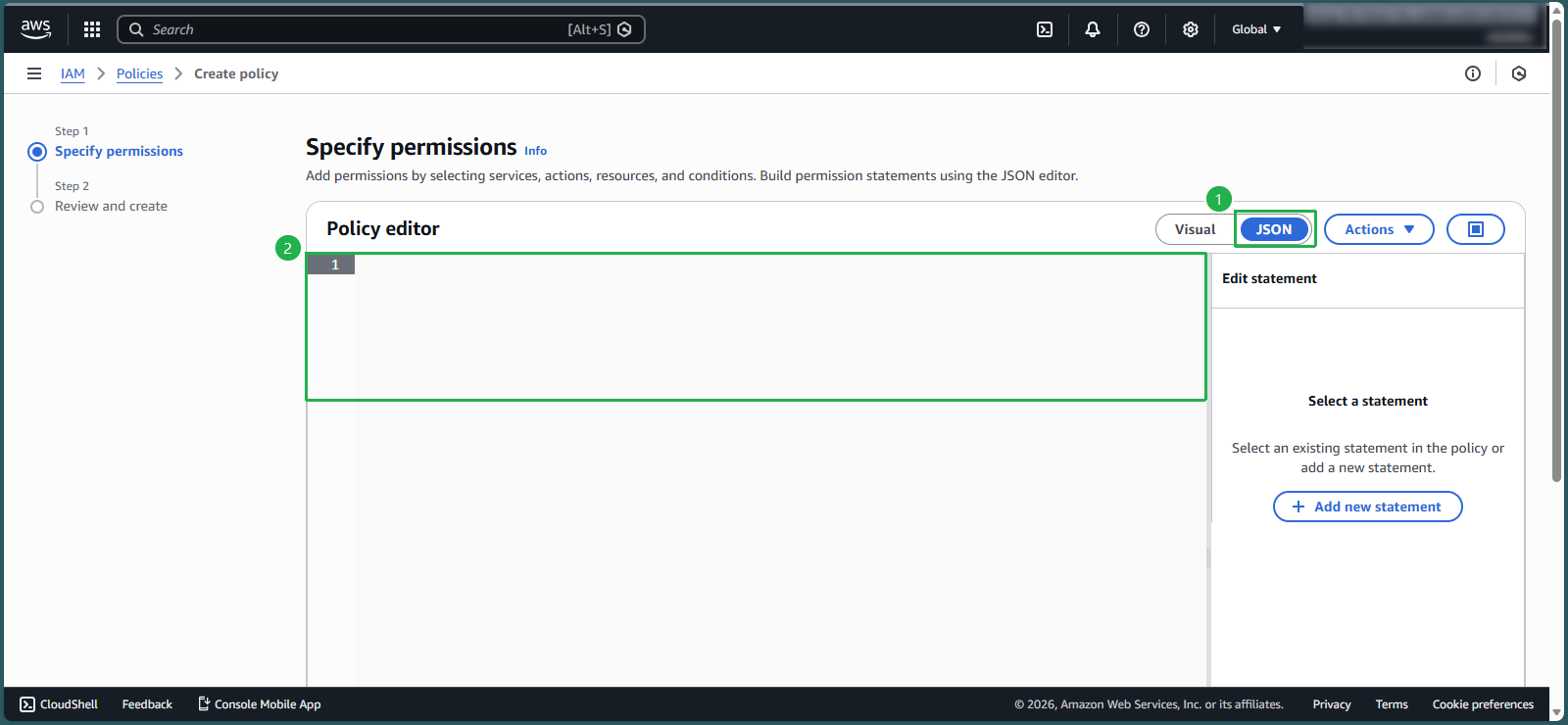
- Copy and paste the following policy document:
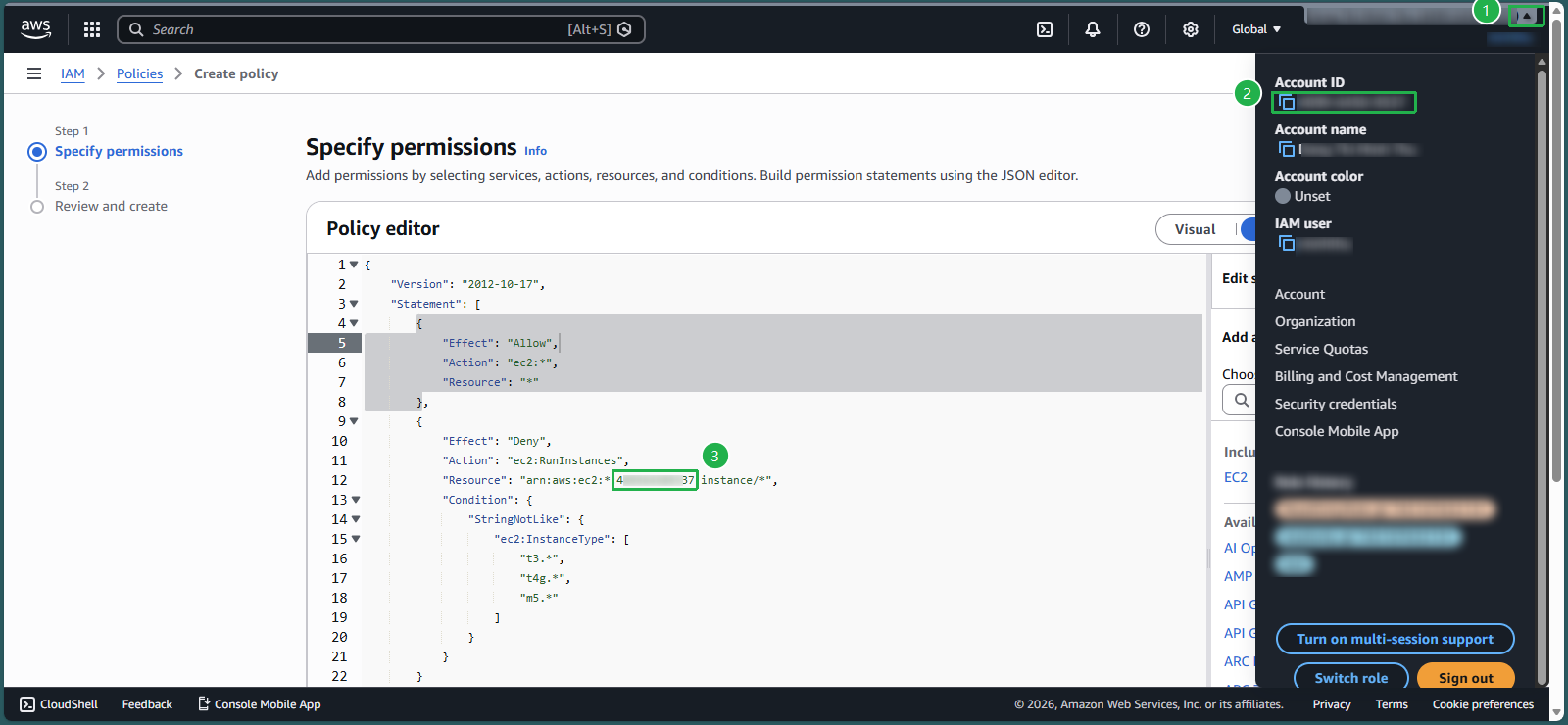
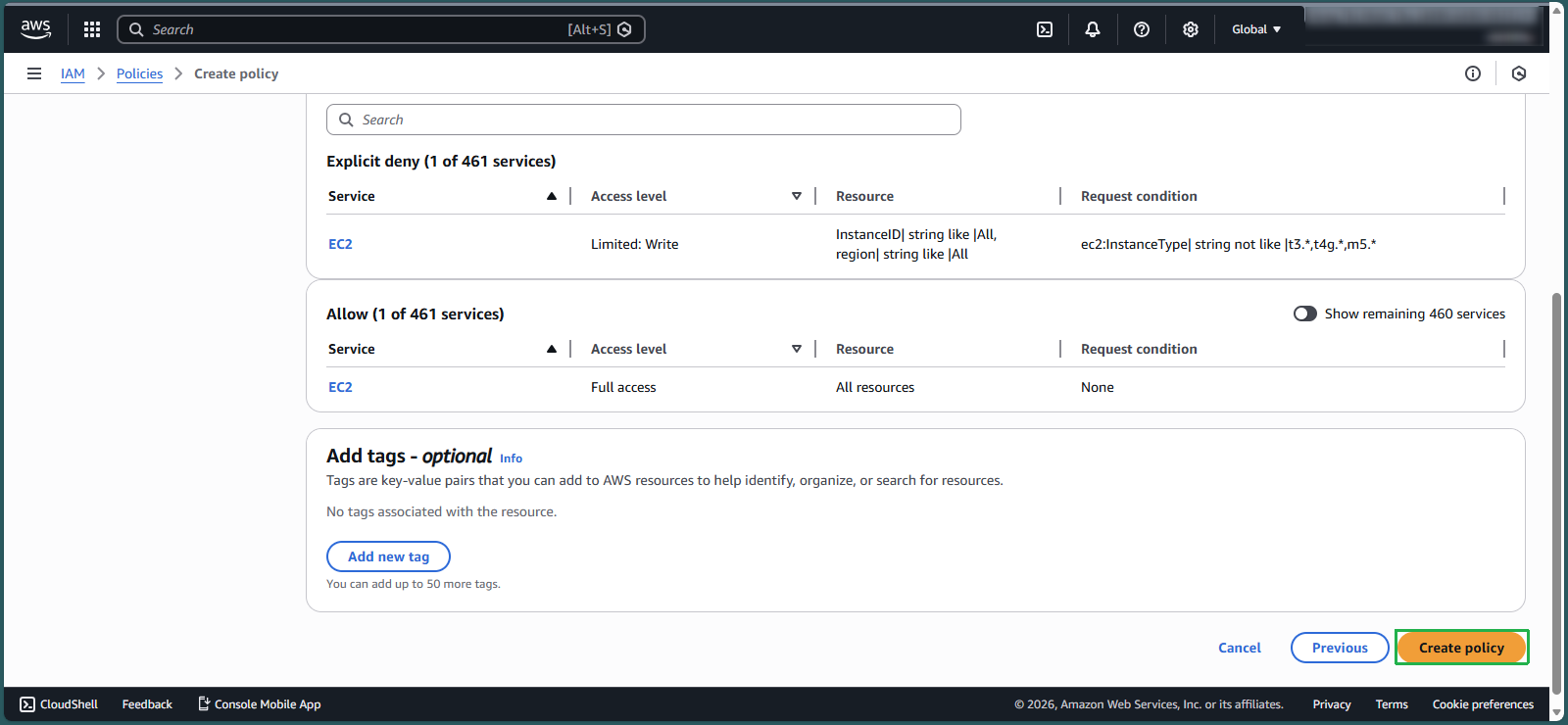
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": "ec2:*", "Resource": "*" }, { "Effect": "Deny", "Action": "ec2:RunInstances", "Resource": "arn:aws:ec2:*:148922931563:instance/*", "Condition": { "StringNotLike": { "ec2:InstanceType": [ "t3.*", "t4g.*", "m5.*" ] } } } ] }- In the AWS Management Console search box, enter
🔒 Security Note: Replace the account ID (148922931563) in the Resource ARN with your own AWS account ID. You can copy your account ID by clicking the account dropdown in the top navigation bar.
Scroll down and click Next to go to Step 2: Review and create.
Enter the following details:
- Policy name:
EC2_FamilyRestrict - Description:
Restrict EC2 instances to t3, t4g and m5 families only
- Policy name:
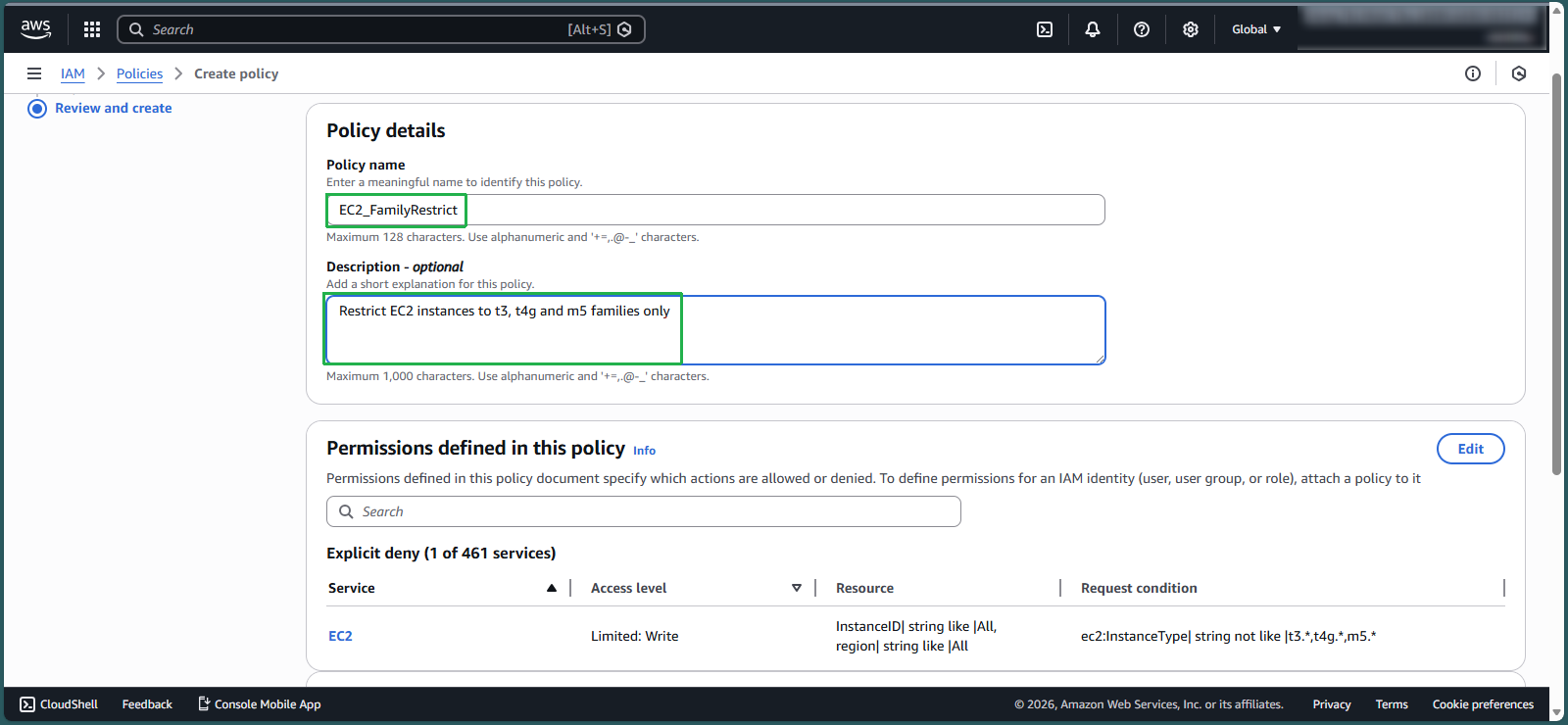
- Review and click Create policy
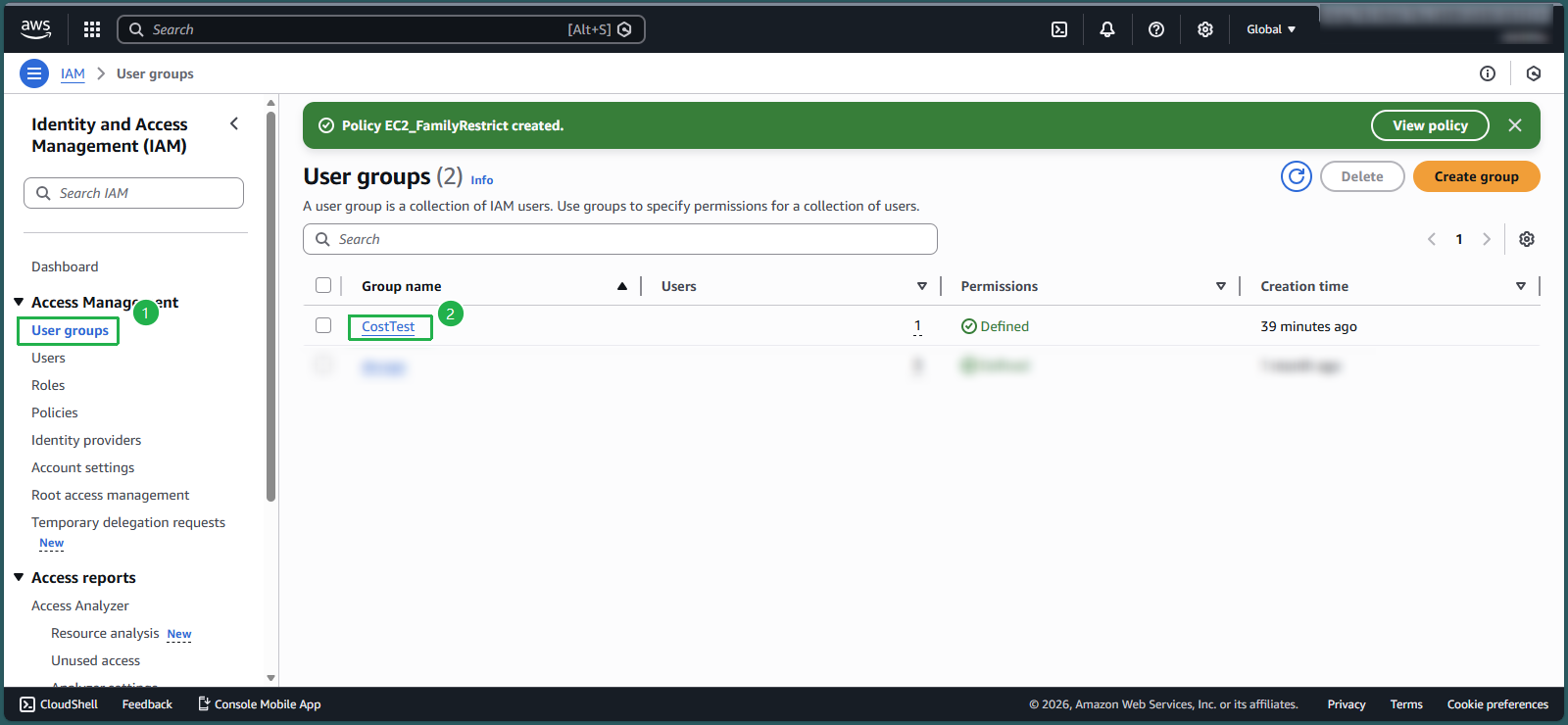
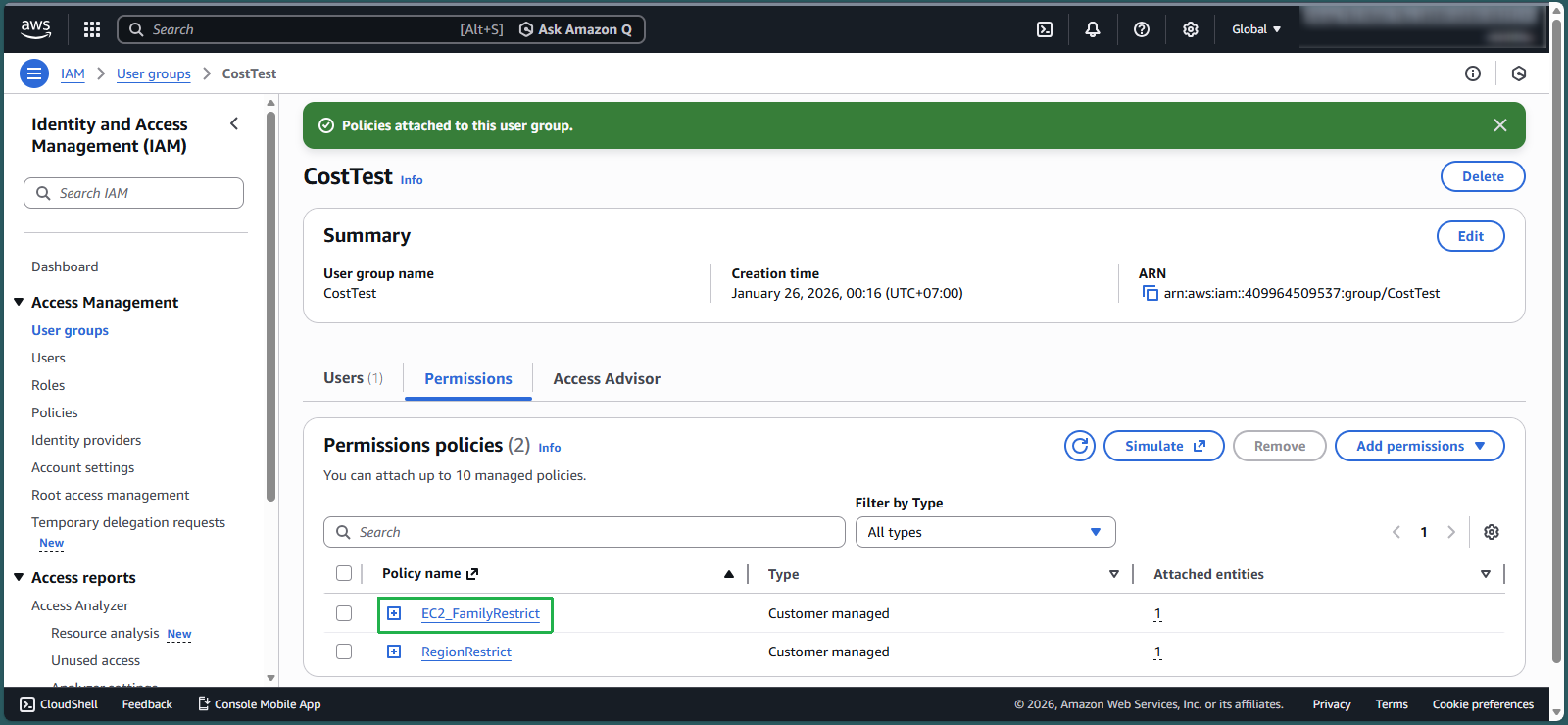
Attach the Policy to an IAM Group
- In the IAM console, select User groups from the navigation pane
- Select the CostTest group
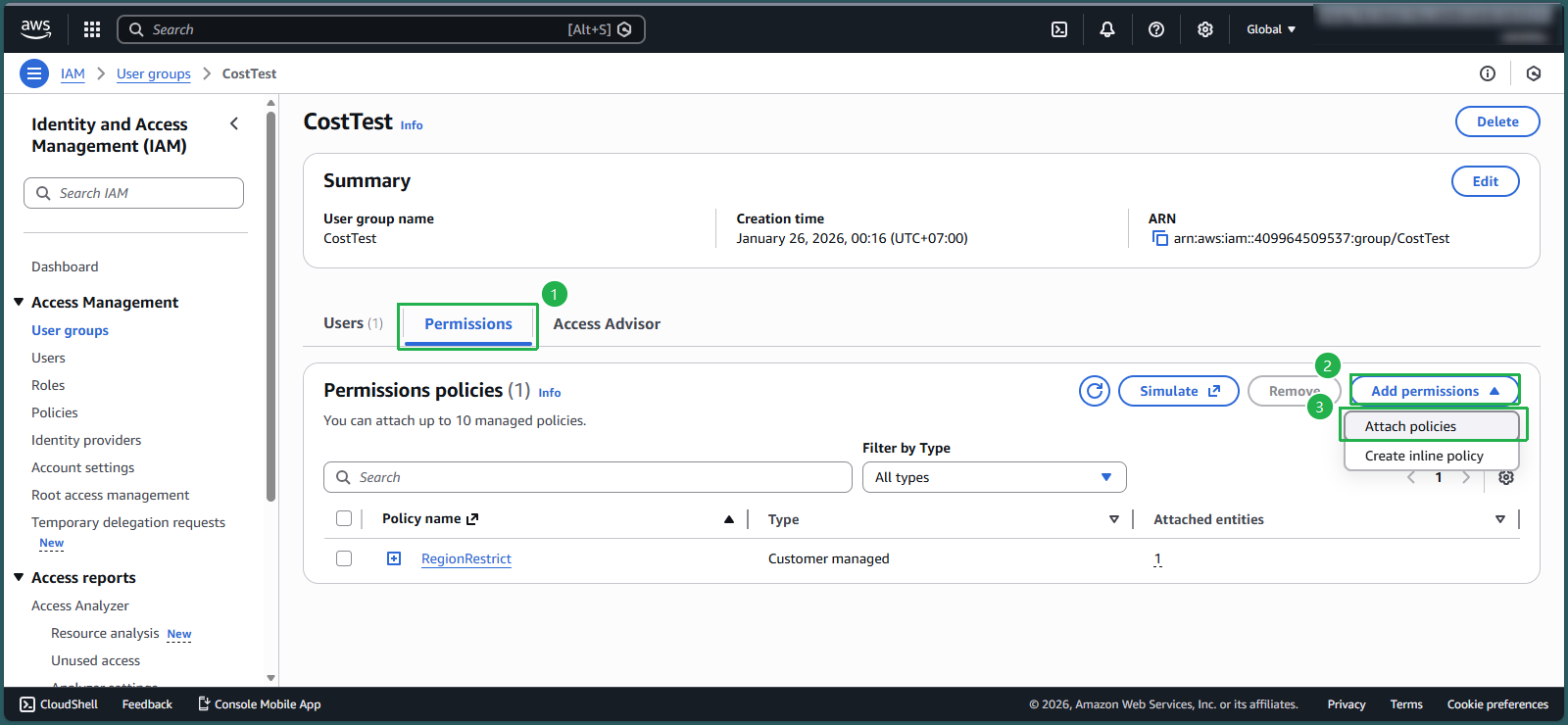
Select the Permissions tab
Click Add permissions, then select Attach policies
- In the search box, enter
EC2_FamilyRestrict - Select the checkbox next to the policy, then click Attach policies
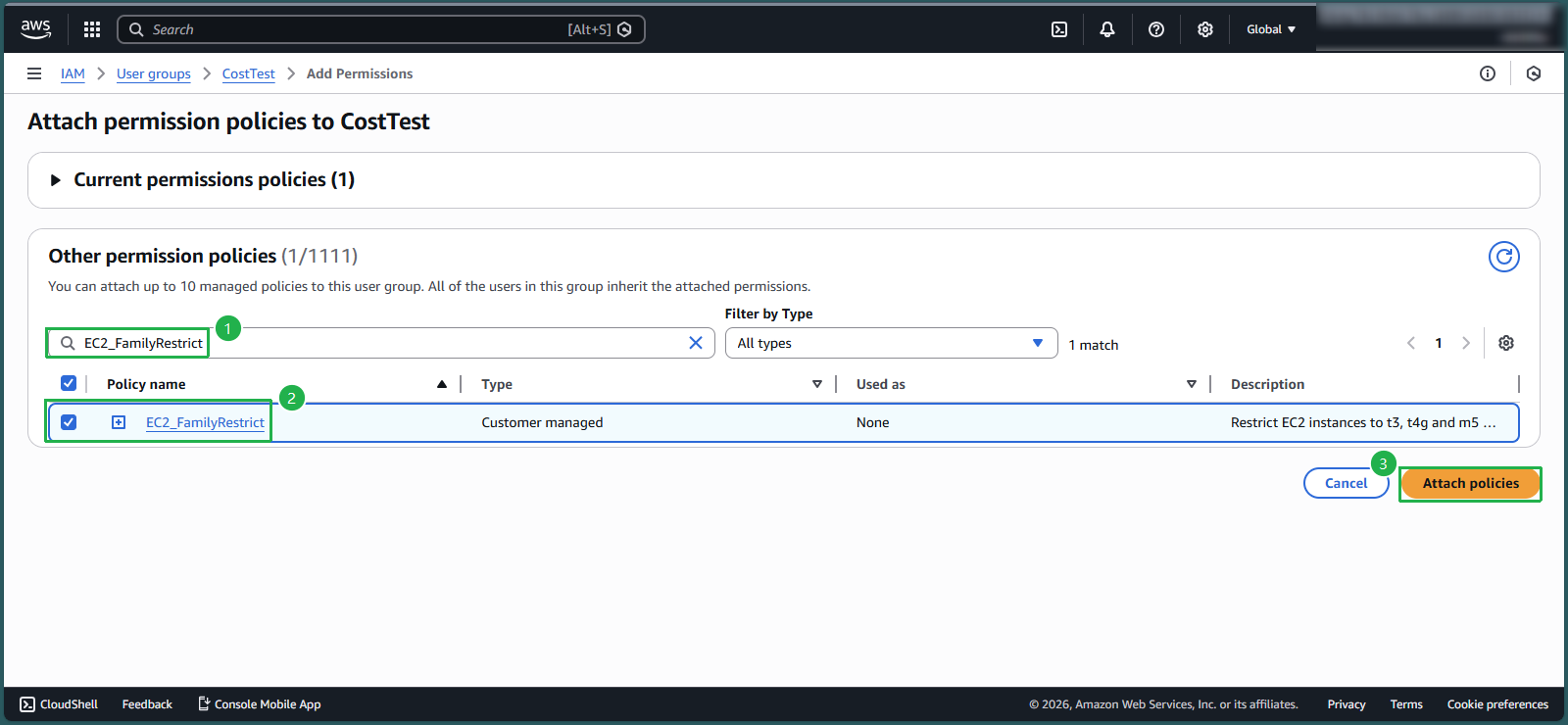
- Review the attached policies
- The group now has both the EC2_FamilyRestrict policy and the RegionRestrict policy from lab 8.1
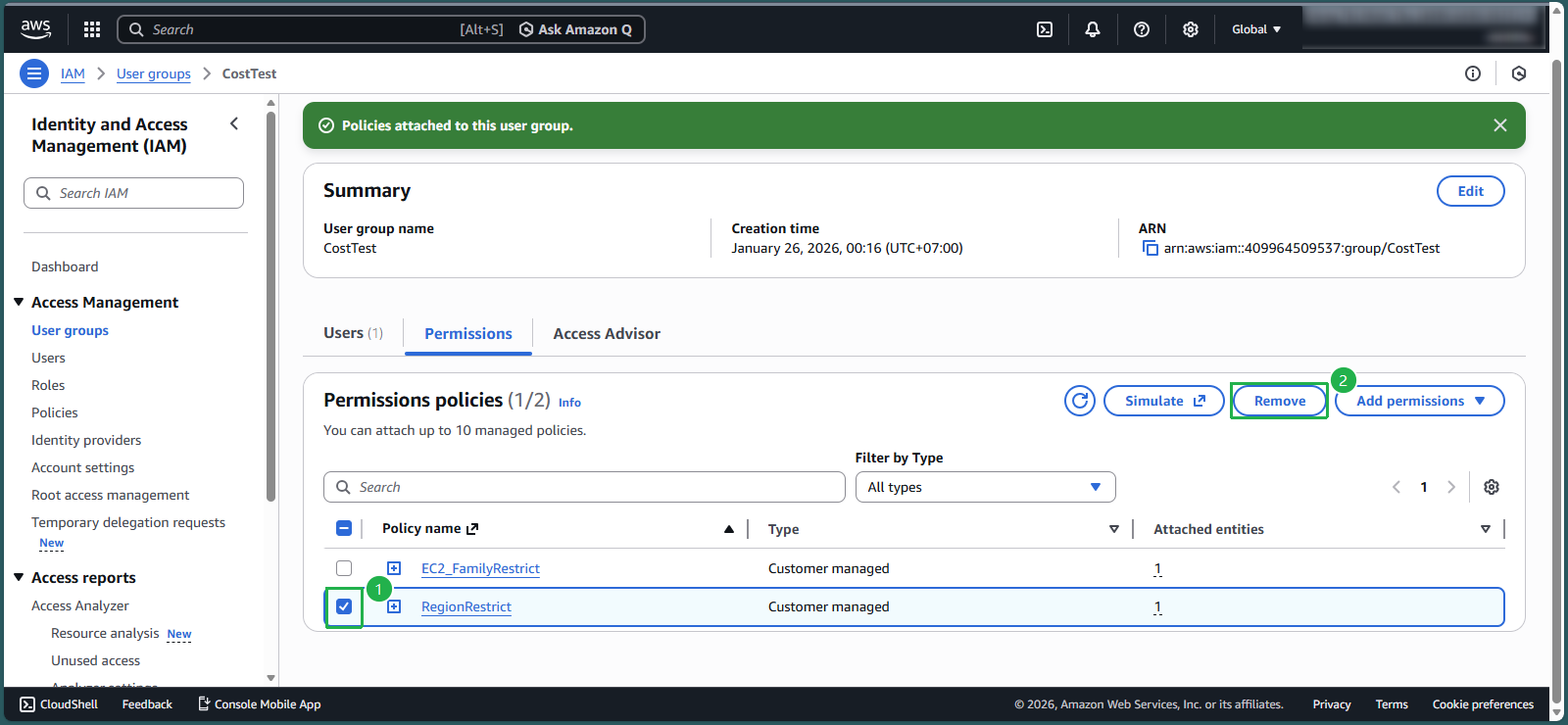
- To follow the principle of least privilege, remove the RegionRestrict policy:
- Select the checkbox next to the policy
- Click Remove
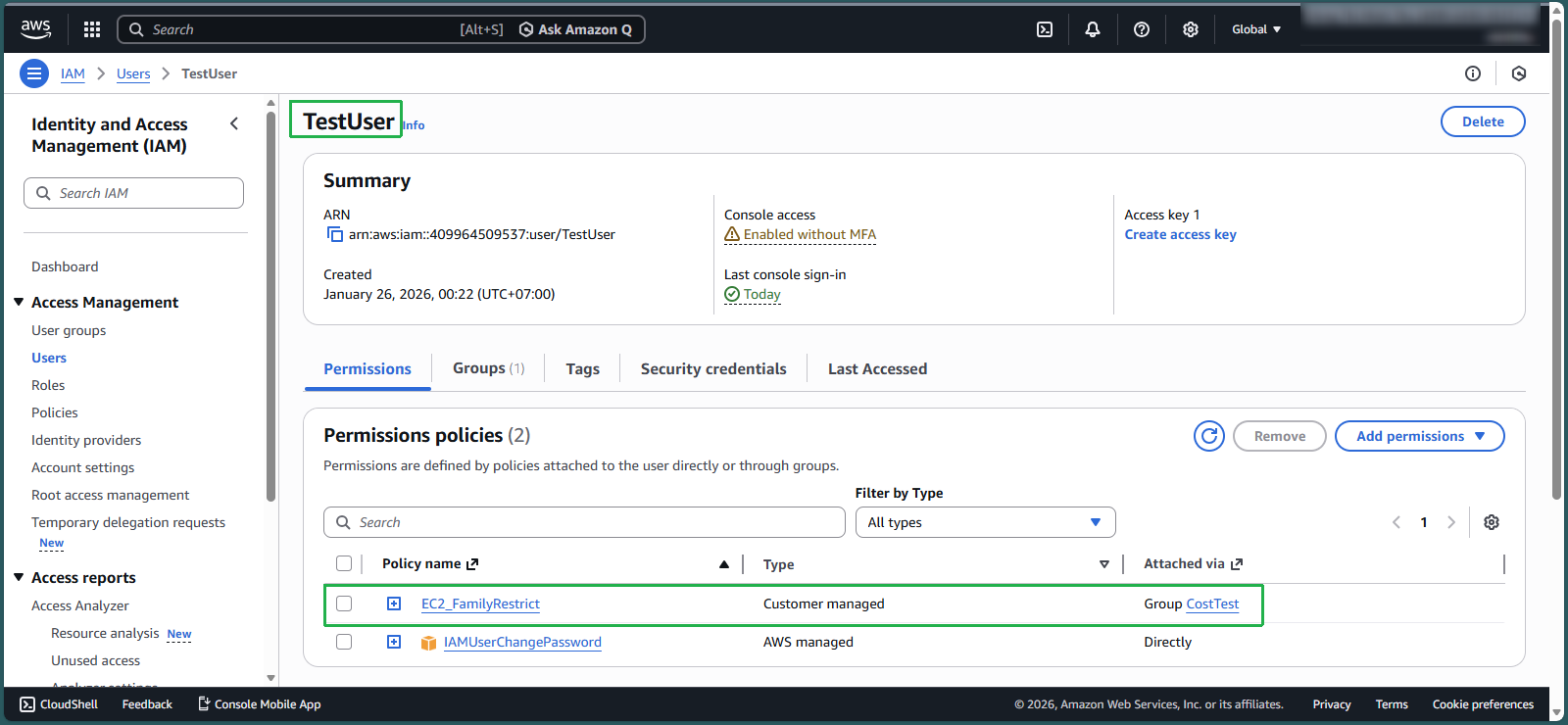
- Verify user permissions:
- Navigate to Users
- Select TestUser
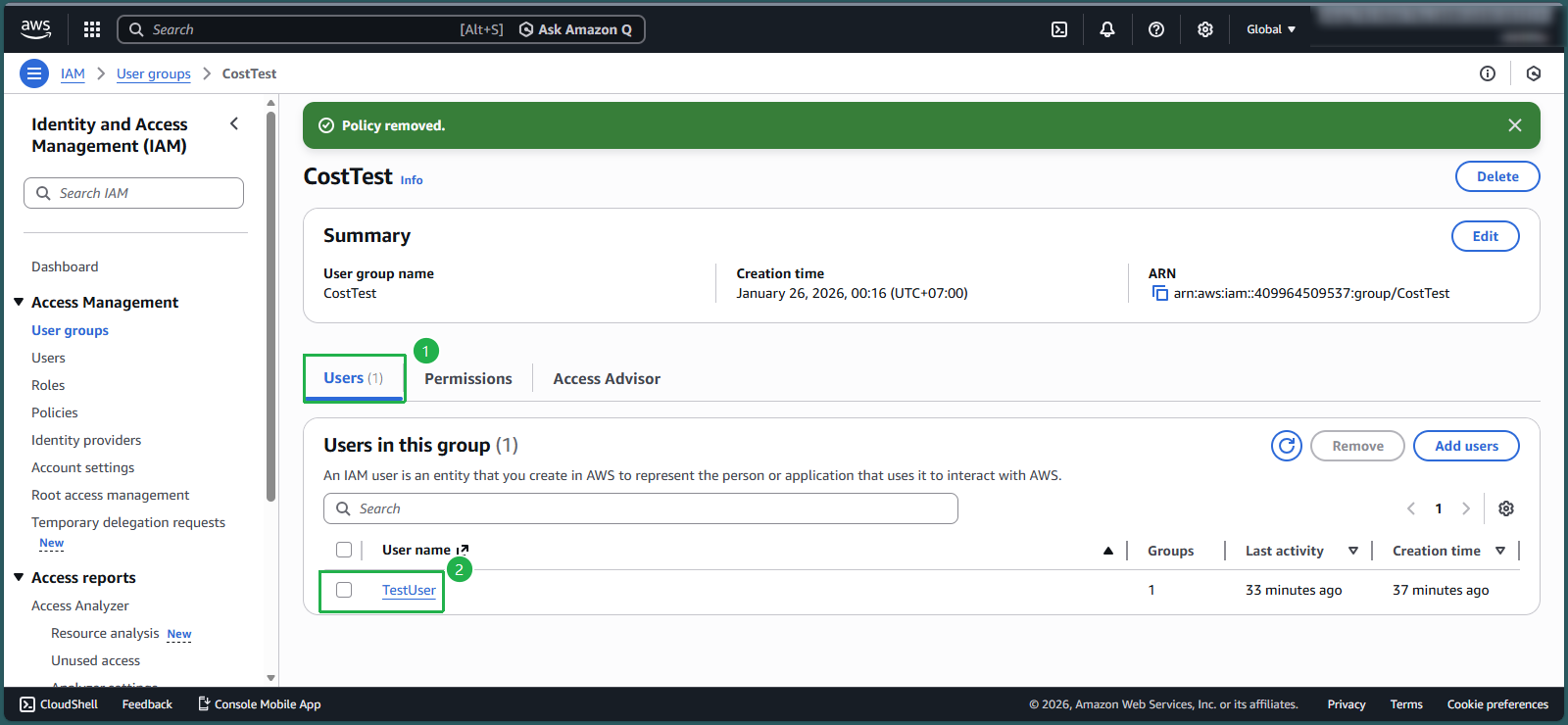
- Confirm that the EC2_FamilyRestrict policy is attached via the CostTest group
- Note that the policy is inherited through group membership rather than direct attachment
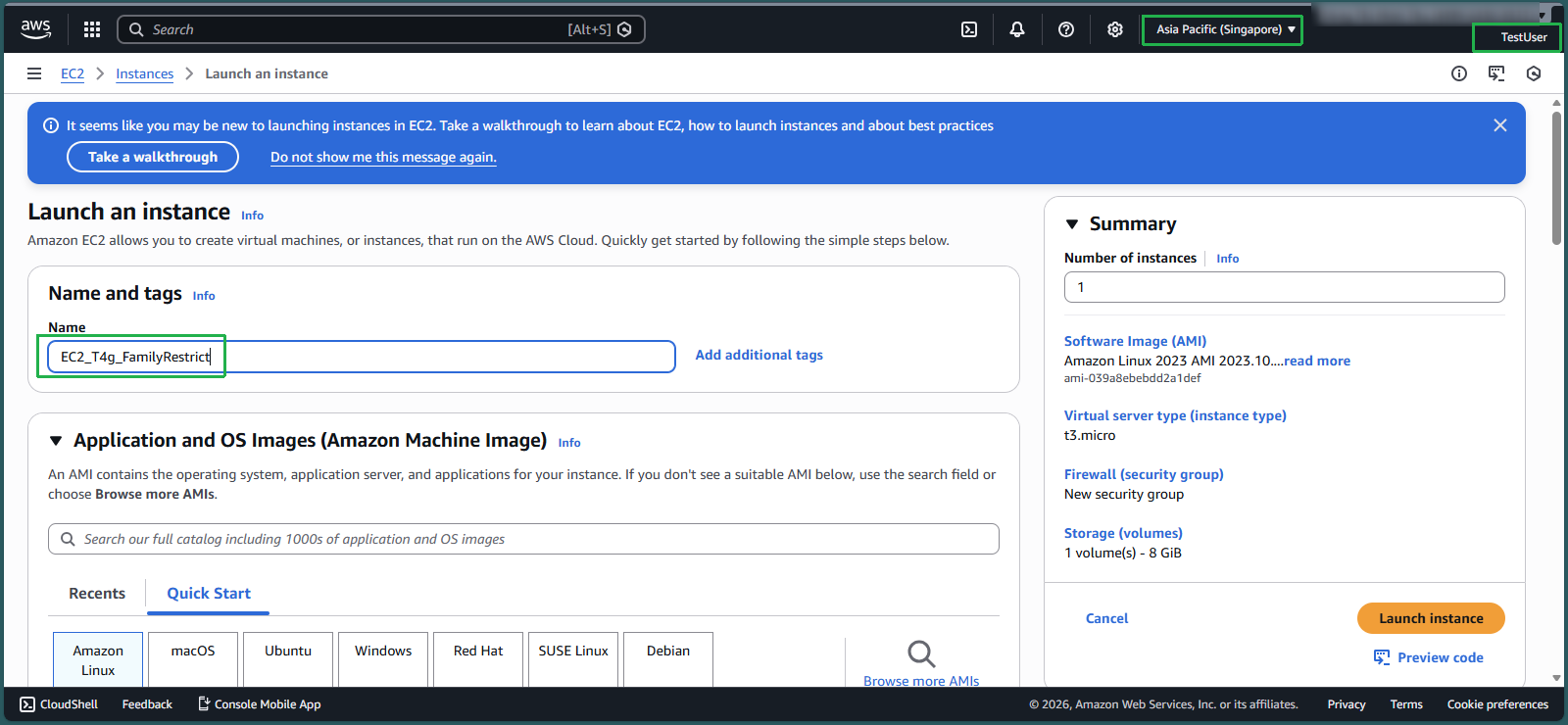
Test Allowed Instance Family: T4g
- Sign in to the AWS Management Console as TestUser
- Ensure you’re in the Singapore Region
- Search for and select EC2
- Click Launch instance
- Enter
EC2_T4g_FamilyRestrictas the instance name
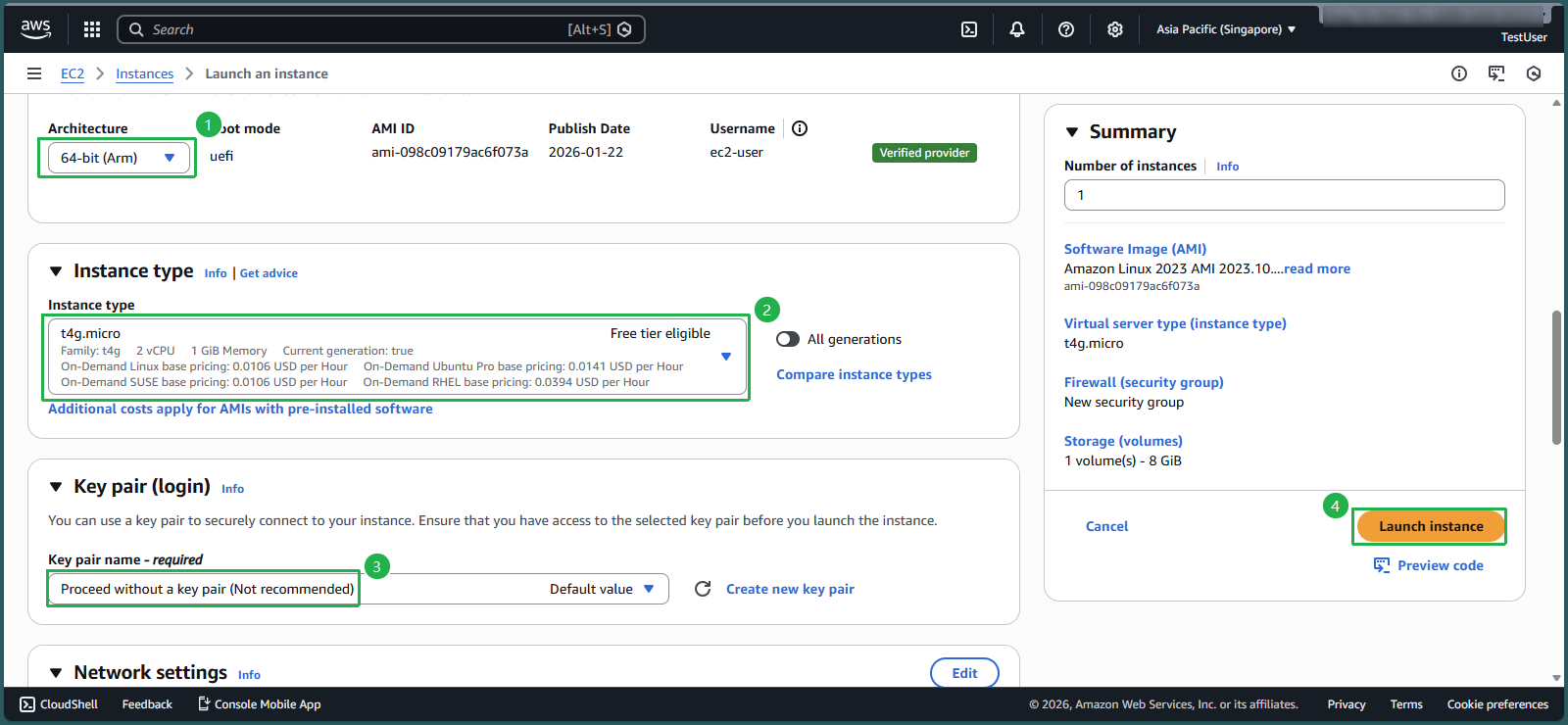
- Under Architecture, select 64-bit(Arm)
- For Instance type, select t4g.micro
- Under Key pair, select Proceed without a key pair
- Click Launch instance
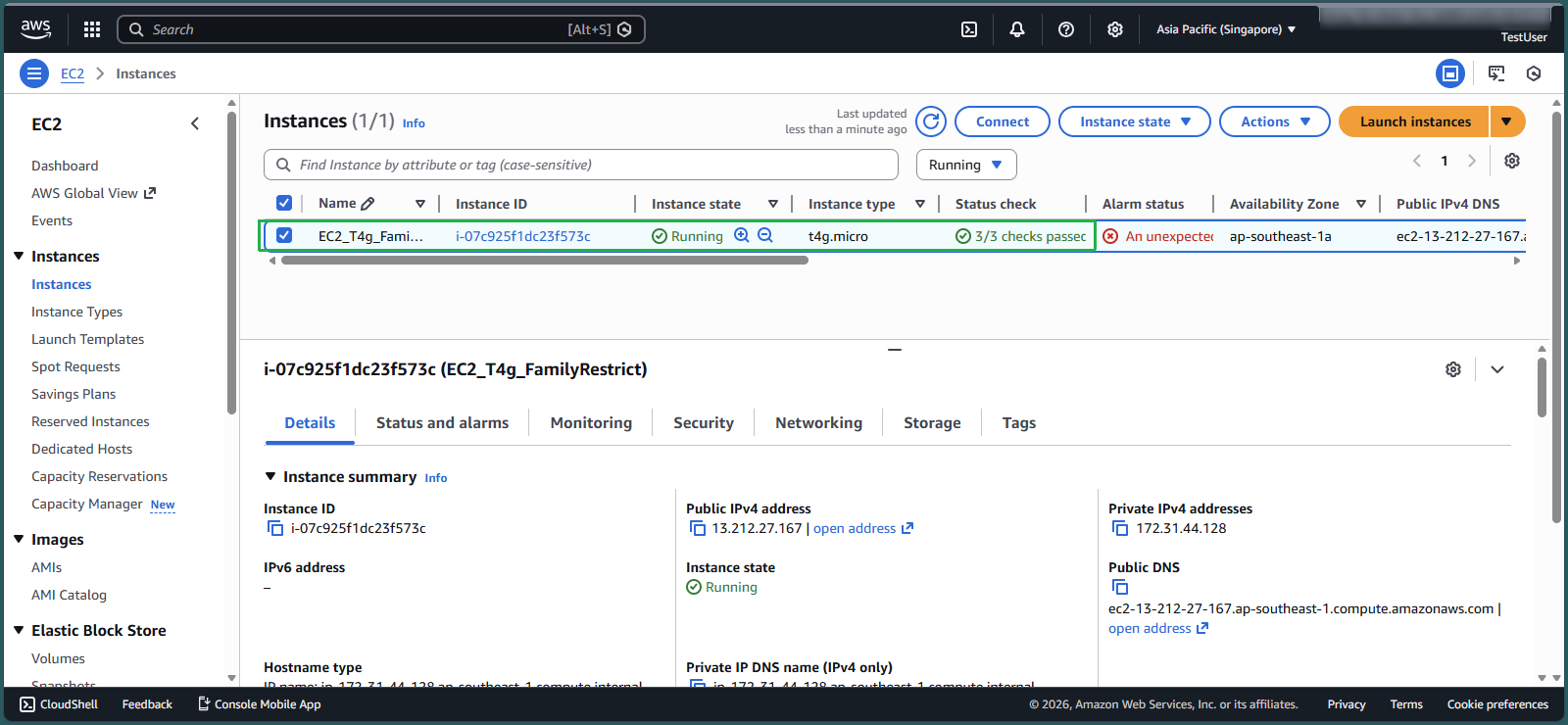
- Click the Instance ID of the newly created instance
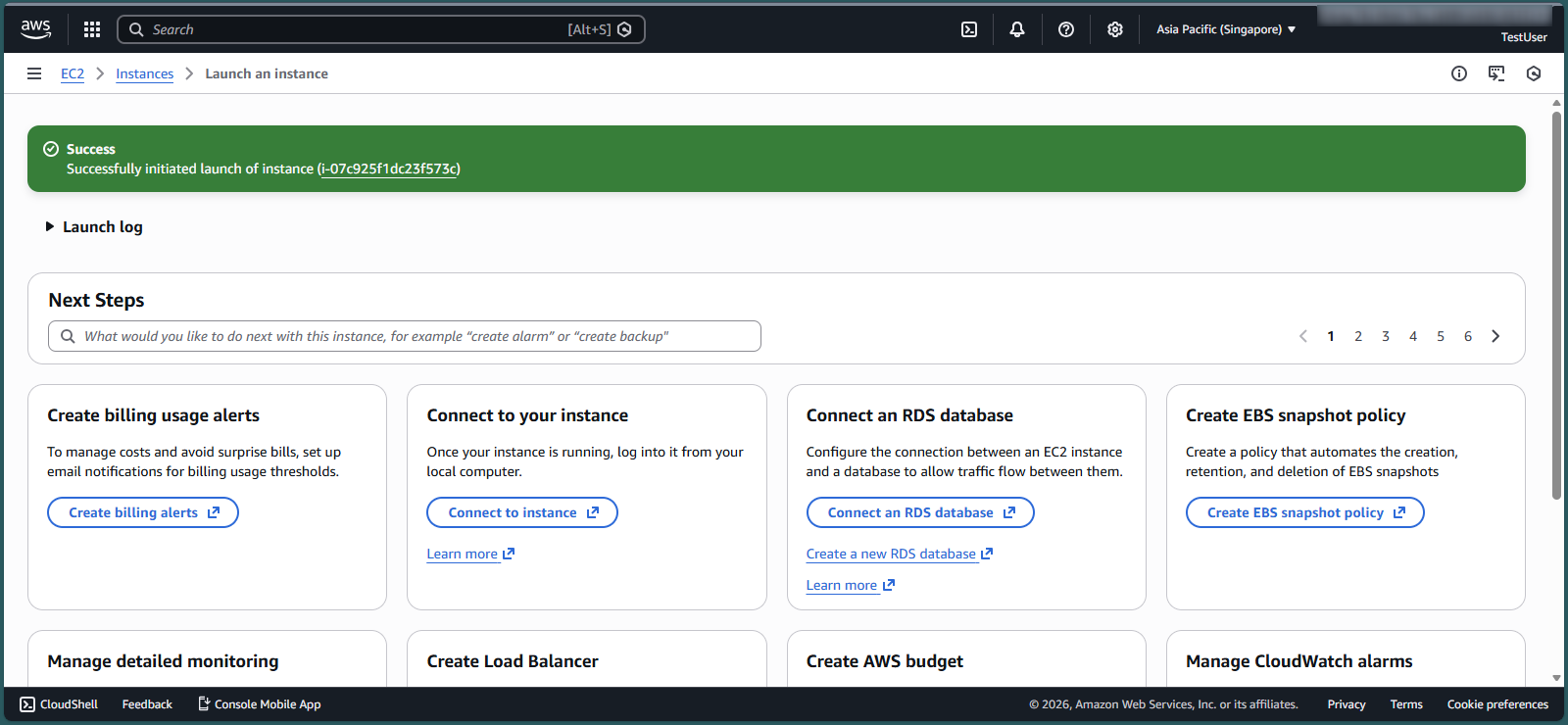
- Verify that the T4g instance was successfully created
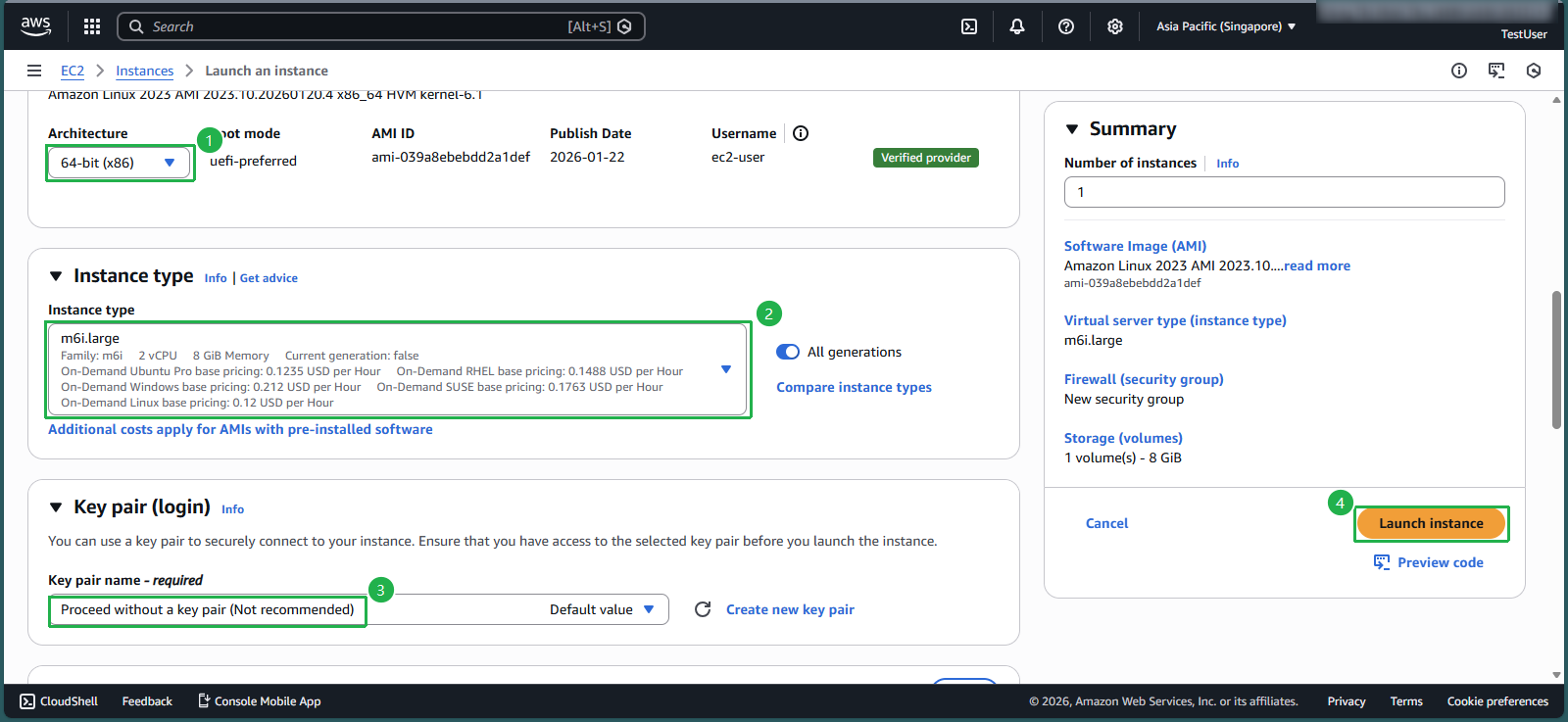
Test Denied Instance Family: M6i
- Click Launch instance
- Enter
EC2_M6i_FamilyRestrictas the instance name
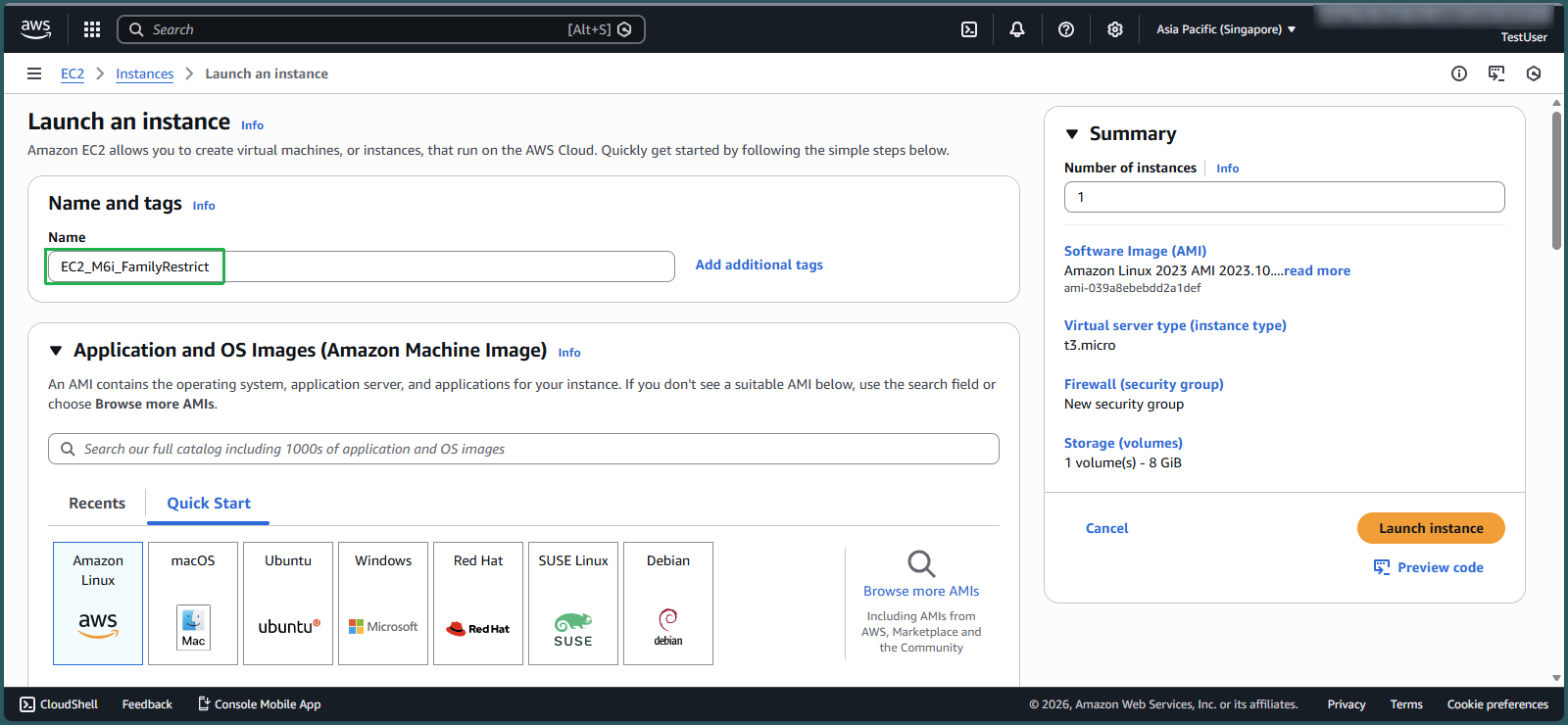
- Keep the default 64-bit(x86) architecture
- For Instance type, select m6i.large
- Under Key pair, select Proceed without a key pair
- Click Launch instance
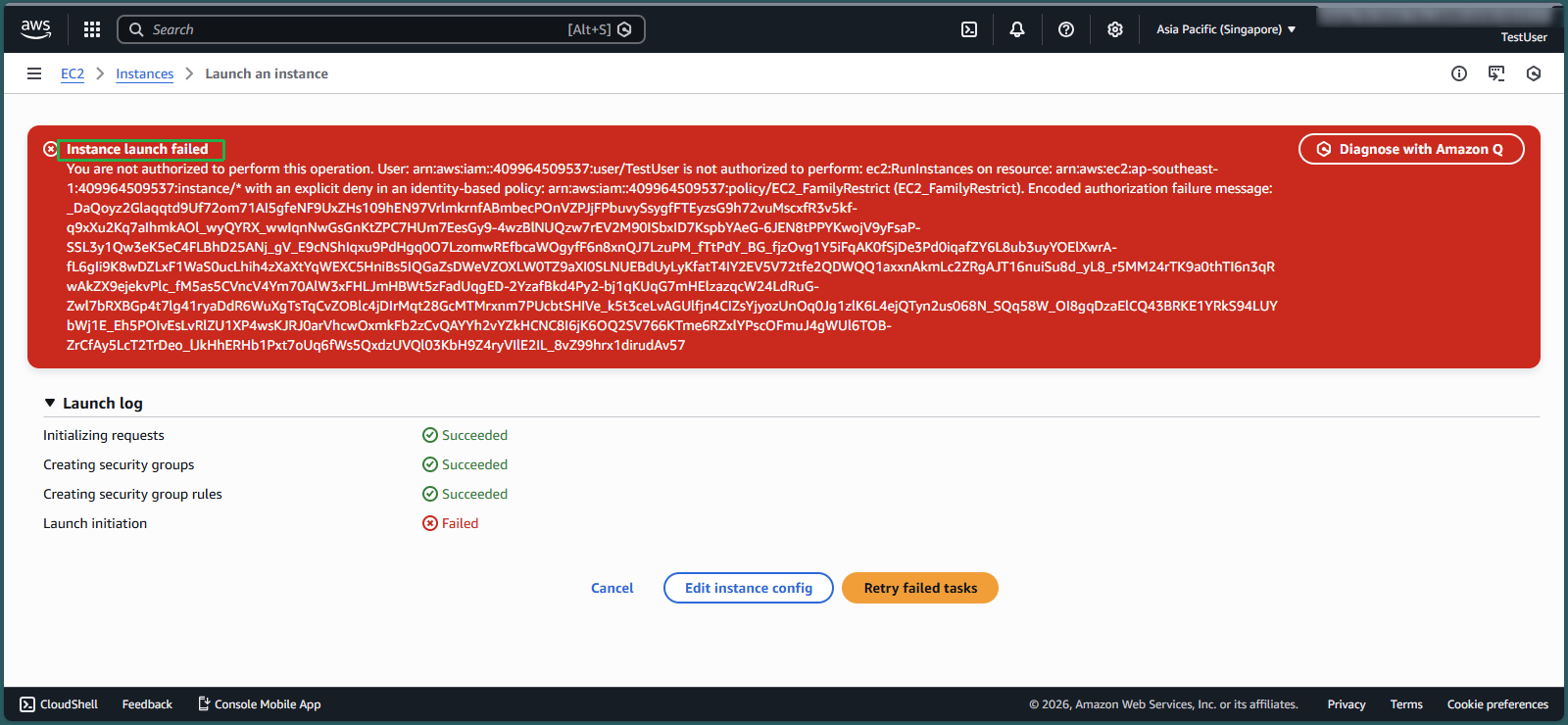
- Observe the Instance launch failed error message
- This confirms that the IAM policy is correctly preventing the launch of non-approved instance families
Additional Testing
For complete verification, you can repeat step 5 with T3 and M5 instance families to confirm they are allowed by the policy.
⚠️ Warning: Remember to terminate any test instances after verification to avoid unnecessary charges. The IAM policy restricts which instance types can be launched but doesn’t prevent charges for running instances.